Computers, Software
The Online world has actually allowed individuals to share themselves freely online, with lots of people using a nickname when producing accounts or publishing things online in order to remain confidential and also safeguard their personal privacy from those looking to track or get more insight about them. Yet with more pressure being placed upon individuals on-line for them to validate identity and also be more clear with what info they give – some reputable, while various others might result in lowered availability of nicknames or various other types of privacy online – individuals need a better method of remaining anonymous in order to secure their privacy when engaging online with others online.
Are Pseudonyms Allowed on Social Media? The issue of whether individuals should utilize pen names on social networks has actually long been controversial. Some argue that utilizing their real names ought to constantly be preferred, while others take into consideration being able to pick from amongst a variety of stage names an indispensable aspect of making use of these systems for service and also leisure.
A pseudonym is a make believe name made use of to shield one’s identity when talking or writing out in public, frequently made use of for creating purposes or public life. There may be various reasons for selecting to make use of one, consisting of anxiety of professional or individual consequences from what one writes or releases. Pseudonymous writing has actually long prevailed, from George Eliot and Mark Twain composing under their pen names to Publius supporting in Federalist Papers or Junius composing letters to Public Advertiser in 18th century London.
On the internet privacy has been an invaluable boon to free speech, however it comes with dangers. Individuals making use of professional names risk of being identified and targeted by any person seeking injury; furthermore there might be security worries concerning nicknames as cyberpunks or malicious actors might use them to gain access to personal data or even steal identifications.
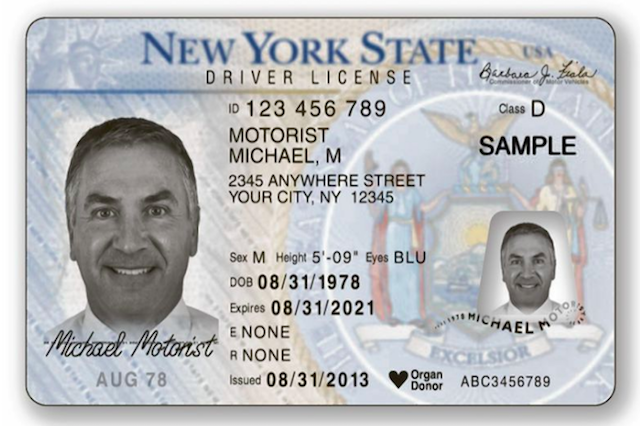
Some have asserted the necessity of using real names when commenting online web content such as news short articles. Their thinking depends on the idea that any kind of dynamic debate with individuals who may bully or pester others online can not take area if no web link can be drawn in between their offline identities and on-line ones. Many individuals realize that, in some cases it might be very necessary to sign up on online sites with pretended information and lots of people might want to think about idaho fake drivers License…
Is it really so basic to link someone’s on the internet as well as offline lives? A research performed by a comment organizing service discovered that the majority of people who choose to use professional names weren’t trying to hide anything; rather they merely preferred more control over what information was shared among area members. Instead of seeing this issue as either/or, probably rather creating policies which promote nicknames while giving individuals liberty in picking when sharing info is ideal or unacceptable.
Cyber hazards come from lots of sources, each looking to acquire personal information (PI) for benefit or exploitation. Internet privacy is a subset of the larger world of information privacy that covers the collection, usage, and safe storage of PI usually.
A Pew Research Institute research study discovered that controlling PI on line is “extremely crucial” to 72% of Americans. According to another Pew research study, 77% of Americans have done something about it to preserve their privacy– erasing cookies, securing e-mail, and securing their IP address.
Digital footprints are all over. Each time you visit an internet site, enter your credit or debit card info, register for an account, provide your email, submit online kinds, post on social media, or store images or documents in cloud storage, you are launching personal information into cyberspace. Just who, aside from the desired recipient, will have or get access to the details you supplied? Will it be shown other celebrations? Your PI may be shared in ways you do not expect or are unaware of. Your info may be at some danger since even the best details security programs are not 100% ensured. Site registration is an annoyance to most people. That’s not the worst aspect of it. You’re generally increasing the risk of having your info taken. But, often it may be needed to sign up on sites with make-believe identity or you may wish to consider fake Indiana Drivers license !
There is no single law controling online privacy. Some key federal laws affecting online privacy include:
The Federal Trade Commission Act (FTC) [1914]– manages deceptive or unreasonable industrial practices. The FTC is the main federal regulator in the privacy area and brings enforcement actions versus companies. This consists of failing to abide by published privacy policies and stopping working to sufficiently safeguard individual details.
Electronic Communications Privacy Act (ECPA) [1986] – secures specific wire, oral, and electronic interactions from unauthorized interception, disclosure, access, and use.
— makes illegal certain computer-related activities involving the unapproved gain access to of a computer to acquire certain info, get or defraud anything of worth, transmit harmful items, or traffic in computer passwords.
Kid’s Online Privacy Protection Act (COPPA) [1998]– needs particular site and online service providers to obtain proven adult permission before gathering, using, or revealing personal info from minors under the age of 13. It likewise requires web sites to post an online privacy policy, gather only the personal details needed, and develop and keep affordable security measures.
Controlling the Assault of Non-Solicited Pornography and Marketing Act (CAN-SPAM Act) [2003]— governs sending out unsolicited industrial email and forbids deceptive header info and misleading subject lines. It likewise requires senders to reveal specific information, consist of a legitimate opt-out mechanism, and it creates criminal and civil penalties for offenses.
Financial Services Modernization Act (GLBA) [1999]– controls the collection, usage, and disclosure of personal info collected or held by financial institutions and needs consumer notices and a composed details security program.
Fair and Accurate Credit Transactions Act (FACTA) [2003]– needs financial institutions and financial institutions to maintain written identity theft avoidance programs.
Lots of states have also embraced laws impacting online privacy, for instance, consumer protection statutes, laws that safeguard specific classifications of PI, info security laws, and data breach alert laws. In addition to adhering to these laws and executing robust details security programs, there are actions organizations can take to help reduce cybersecurity risks.
Client, customer, and staff member personal info in your ownership can be based on a data breach in a myriad of ways. E-mail addresses, banking, passwords, physical addresses, contact number and more can inadvertently discover their methods to scammers, hackers, undesired online marketers, and more. The majority of compliance and legal location employees have little idea how to go carry out information defense from web hazards. Quite a few individuals realize that, often it might be very necessary to register on websites with invented specifics and many people may wish to consider Colorado Fake Drivers License..!
 Something your company can do is establish an Internet privacy quick reference playbook that is quickly available to workers. It can offer details and best practices to follow for your particular location.
Something your company can do is establish an Internet privacy quick reference playbook that is quickly available to workers. It can offer details and best practices to follow for your particular location.
Six months ago privacy data consumer advocates announced proposed upcoming legislation to establish an online privacy law setting tougher privacy requirements for Facebook, Google, Amazon and lots of other online platforms. These businesses gather and use vast amounts of customers individual information, much of it without their knowledge or real permission, and the law is intended to guard against privacy damages from these practices.
 The higher requirements would be backed by increased penalties for disturbance with privacy under the Privacy Act and greater enforcement powers for the federal privacy commissioner. Major or duplicated breaches of the law might bring penalties for business.
The higher requirements would be backed by increased penalties for disturbance with privacy under the Privacy Act and greater enforcement powers for the federal privacy commissioner. Major or duplicated breaches of the law might bring penalties for business.

Nevertheless, relevant business are likely to attempt to prevent obligations under the law by drawing out the procedure for signing up the law and drafting. They are likewise likely to attempt to exclude themselves from the code’s coverage, and argue about the meaning of personal information.
The present meaning of individual details under the Privacy Act does not clearly consist of technical information such as IP addresses and gadget identifiers. Updating this will be crucial to guarantee the law is effective.
The law would target online platforms that “gather a high volume of personal information or trade in individual info”, consisting of social networks networks such as Facebook; dating apps like Bumble; online blogging or online forum websites like Reddit; video gaming platforms; online messaging and video conferencing services such as WhatsApp, Zoom and data brokers that sell individual information as well as other big online platforms that collect personal details.
The law would impose higher standards for these business than otherwise apply under the Privacy Act. The law would likewise set out information about how these organisations must fulfill obligations under the Privacy Act. This would consist of greater standards for what constitutes users consent for how their data is utilized.
The government’s explanatory paper states the law would require approval to be voluntary, notified, unambiguous, specific and current. The draft legislation itself does not really state that, and will require some modification to achieve this.
This description makes use of the definition of consent in the General Data Protection Regulation. Under the proposed law, customers would have to give voluntary, informed, unambiguous, existing and particular consent to what business do with their information.
In the EU, for example, unambiguous consent indicates a person needs to take clear, affirmative action– for example by ticking a box or clicking a button– to consent to a use of their information. Approval should likewise be specific, so business can not, for instance, require customers to grant unassociated usages such as marketing research when their information is only required to process a specific purchase.
The consumer supporter suggested we need to have a right to erase our personal information as a means of lowering the power imbalance in between consumers and large platforms. In the EU, the “right to be forgotten” by search engines and the like is part of this erasure. The federal government has not adopted this recommendation.
The law would include a commitment for organisations to comply with a customer’s reasonable demand to stop using and disclosing their personal data. Companies would be enabled to charge a non-excessive charge for satisfying these requests. This is an extremely weak version of the EU right to be forgotten.
For instance, Amazon currently specifies in its privacy policy that it utilizes consumers individual information in its advertising service and discloses the information to its large Amazon.com corporate group. The proposed law would mean Amazon would have to stop this, at a consumers request, unless it had sensible grounds for refusing.
Ideally, the law ought to likewise enable customers to ask a company to stop gathering their individual details from third parties, as they presently do, to construct profiles on us.
The draft bill also includes an unclear arrangement for the law to include securities for kids and other susceptible individuals who are not capable of making their own privacy decisions.
A more questionable proposition would require brand-new approvals and verification for kids utilizing social networks services such as Facebook and WhatsApp. These services would be required to take affordable steps to confirm the age of social media users and obtain adult consent prior to collecting, using or divulging individual information of a kid under 16 of age.
A key tactic business will likely use to avoid the new laws is to declare that the information they utilize is not truly personal, considering that the law and the Privacy Act only apply to personal details, as defined in the law. Some individuals recognize that, in some cases it may be very necessary to register on sites with fictitious specifics and many people may wish to think about Fake Ohio Drivers License.!
The companies may declare the data they collect is just linked to our private gadget or to an online identifier they’ve designated to us, instead of our legal name. The result is the same. The information is utilized to develop a more comprehensive profile on a specific and to have effects on that person.
The United States, needs to update the definition of personal information to clarify it consisting of data such as IP addresses, device identifiers, location information, and any other online identifiers that might be utilized to determine a specific or to communicate with them on a private basis. If no person is identifiable from that information, data must just be de-identified.
The federal government has vowed to provide tougher powers to the privacy commissioner, and to hit business with harder penalties for breaching their obligations as soon as the law enters effect. The optimum civil charge for a repetitive and/or serious disturbance with privacy will be increased approximately the comparable penalties in the Consumer security Law.
For people, the optimum charge will increase to more than $500,000. For corporations, the optimum will be the higher of $10 million, or 3 times the value of the benefit gotten from the breach, or if this worth can not be figured out 12% of the company’s yearly turnover.
The privacy commission might likewise issue violation notifications for failing to supply appropriate information to an investigation. Such civil penalties will make it unneeded for the Commission to resort to prosecution of a criminal offence, or to civil litigation, in these cases.
The tech giants will have plenty of chance to create hold-up in this process. Companies are likely to challenge the material of the law, and whether they ought to even be covered by it at all.
Fictitious names are presumed names, pseudonyms other than their proper names for an entity or individual. Some states mandate businesses submit fictitious names to expose who owns and runs their businesses. designations
Some company owner choose fictitious names to interest specific markets or signal status, style and professionalism; others are needed by law to do so.
As part of starting your own service, it is necessary to understand whether filing for DBA in your state is required prior to starting operations. At Nav, they use resources to help with this step if relevant as well as finding service credit cards to money its development if needed.
If you have experienced unexpected charges on your bank, credit card, or other monetary accounts without authorization, it could be the outcome of identity theft. Bad guys utilize your individual data to open credit cards, loans and even submit deceptive tax returns in your name; lenders may even send out notifications that an identity thief has actually filed suit against you; while cyber attacks such as “phishing” occur when lawbreakers send emails that look legitimate and request account information (passwords and so on).
![]() Organizations using fictitious names should submit what’s known as a “fictitious name declaration.” This allows customers to call them if issues develop with the business and its ownership, while numerous online users utilize pseudonyms in order to keep their identity personal, such as utilizing an ID instead of their real name when signing onto websites or socials media.
Organizations using fictitious names should submit what’s known as a “fictitious name declaration.” This allows customers to call them if issues develop with the business and its ownership, while numerous online users utilize pseudonyms in order to keep their identity personal, such as utilizing an ID instead of their real name when signing onto websites or socials media.
![]() Privacy in today’s digital world is a problem worth facing, with people requiring to safeguard their personal data such as name and address from cyber-criminals and stalkers. One reliable technique for doing this is utilizing pseudonyms online – these enable users to connect without disclosing their genuine names to others.
Privacy in today’s digital world is a problem worth facing, with people requiring to safeguard their personal data such as name and address from cyber-criminals and stalkers. One reliable technique for doing this is utilizing pseudonyms online – these enable users to connect without disclosing their genuine names to others.
Fictitious names provide a reliable ways of preventing legal name requirements when carrying out business activities, for example by sole owners and partnerships when revealing their organization or getting credit. Fictitious names may also help organizations re-brand or enter brand-new markets more quickly while business filing can permit several restaurants, stores or sites with various brand under one umbrella name without having to establish different legal entities for each. There are so many individuals realize that, sometimes it may be essential to sign up on websites with invented information and lots of people may want to think about Fake Connecticut Drivers License!
A fictitious name can likewise make structure company credit or acquiring service credit cards easier. A lot of states permit services signed up under their DBA name to get credit under it once registered; it’s essential to contact your state department to understand what its procedure appears like in your area; some need renewing registration every now and then or making necessary updates prior to the expiration date or registration modifications, which will keep them certified and avoid their business from falling out of good standing with state guidelines.
Fictitious names been available in numerous kinds; from marketing mottos that catch consumers’ imagination to moniker that represent status or style. Fictitious names should also be signed up with their state of operation to prevent legal problems for companies running under one. Unique and creative names for their business will assist business owners to prevent this commitment and minimize legal concerns on their own and their clients alike.
Susan Jones might call her catering business “Catering Capers,” however to protect her legal rights she should submit a fictitious name statement connecting that brand name with Smith Enterprises as her legal organization name. This provides consumers with access to more details regarding who owns it if there are concerns or need to bring suit against it.
When applying for credit cards for their businesses, service owners should also think about using fictitious names. Fictitious names can help speed up developing your credit faster as lending institutions see it as separate from individual credit. It is recommended to check with the state department concerning how long DBA or fictitious name registration will stay legitimate as it needs to be renewed regularly and some states also require that you recognize what type of entity runs under it when registering your name.
Privacy can possibly be essential in numerous different contexts, consisting of sharing personal information with employees, non-compete agreements and other clauses. Privacy plans offer to protect info that neither you neither your clients or clients want shared publicly, in addition to following professional standards as well as statutory demands.
Via the internet, nicknames offer people a safe means to engage without fear of being linked back to their real identities. Furthermore, professional names permit individuals to prevent revealing individual details like where they attend or live school in addition to age – something which is specifically practical in communities where going over information such as these can impede dialogue or foster biases.
A number of people choose for nicknames when collaborating on innovative projects with others. Friends and partners sometimes collaborate on writing jobs making use of common assumed names; this can assist separate expert from individual work or discover a different style of creating.
Professional names provide privacy when connecting in on the internet discussion forums, emails or data-sharing systems with others that contain identifiable information such as names or header info in packets. While pseudonyms supply some degree of privacy protection, their key function must be individuality when picking one for usage on the internet.
On-line conversations often make use of pen names for anonymity purposes, enabling individuals to articulate their thoughts easily without fear of objection or damage to their reputations. They also allow function playing experiments – for instance, guys might position as women to acquire even more insight right into female viewpoints on certain topics.
Pen names are a significantly usual attribute in literary works, as well as often authors utilize pseudonyms as a means to separate their composing from that of similar authors who share a name – for example J.K. Rowling utilizes Lemony Snicket as her pen name to avoid presumptions connected to her actual name. Some people realize that, in some cases it might be required to register on website or blogs with pseudo information and many people might want to consider virginia fake drivers license..!
Pseudonymity on the web is an indispensable way of securing totally free speech as well as discussion, however it can not assure complete privacy for its customers; numerous Web sites that give pseudonymity still maintain information regarding them which leaves them open to intrusions right into non-public databases, making solid security important when publishing to on-line platforms.
The Web may possibly be an unsafe place, with cybercriminals using nom de plumes to dedicate and also take identities scams. You can lower damage by making certain non-public professional names do not connect back to people’ actual identifications, nor made use of for material small amounts functions.
In contrast to legal names, stage names can not be reasoned from various other information – such as e-mail addresses, IP addresses, blockchain public addresses and individual information – making them a superb way for people that require to talk about debatable or delicate topics without running the risk of safety and security issues or professional effects.
Professional names can also offer useful securities for people with impairments, members of LGBTQ+ areas and abuse survivors. By offering these people anonymity on the internet, stage names enable them to express themselves more openly while getting in touch with individuals that share similar experiences. In addition, their anonymity minimizes risks of discrimination on line and also offerss these people safety from discrimination by protecting their identification on the internet.
A number of individuals use professional name over the internet in order to preserve some degree of separation in between their individual and also specialist lives, securing them from unexpected consequences in their areas or careers. Additionally, nicknames allow individuals freedom of expression and permit individuals to discuss delicate subjects without anxiety of retaliation or reprisal from authorities; political objectors as well as whistleblowers frequently utilize this technique when posting details on-line.
 Professional names can additionally be mistreated for malicious factors; cyber-bullying as well as pedophiles use pen names as cover when preying on targets. To stabilize the potential benefits with their possible abuse, policies that motivate real names while additionally providing solid security actions targeted at preventing harmful uses are important – for example by billing users a charge when utilizing their pen names, or restricting exactly how frequently customers reuse them – or companies could need that all customers present main government identification prior to commenting or uploading anything on the web.
Professional names can additionally be mistreated for malicious factors; cyber-bullying as well as pedophiles use pen names as cover when preying on targets. To stabilize the potential benefits with their possible abuse, policies that motivate real names while additionally providing solid security actions targeted at preventing harmful uses are important – for example by billing users a charge when utilizing their pen names, or restricting exactly how frequently customers reuse them – or companies could need that all customers present main government identification prior to commenting or uploading anything on the web.
Recently a well known Internet security expert just recently spoke with a concerned, personal privacy supporter about what customers can do to protect themselves from federal government and corporate surveillance. Due to the fact that throughout the recent web era, consumers seem progressively resigned to quiting fundamental aspects of their privacy for benefit in using their computer systems and phones, and have reluctantly accepted that being monitored by corporations and even federal governments is simply a fact of modern life.
Internet users in the United States have fewer privacy securities than those in other nations. In April, Congress voted to permit internet service providers to gather and sell their consumers’ searching data. By contrast, the European Union struck Google this summer season with a $3.2 billion antitrust fine.
They spoke about government and business security, and about what worried users can do to secure their privacy. After whistleblower Edward Snowden’s revelations worrying the National Security Agency’s (NSA) mass security operation in 2013, just how much has the federal government landscape in this field altered?
Snowden’s revelations made individuals knowledgeable about what was taking place, however little bit altered as a result. The USA Freedom Act resulted in some small modifications in one specific federal government data-collection program. The NSA’s data collection hasn’t altered; the laws restricting what the NSA can do have not changed; the technology that permits them to do it hasn’t altered. It’s pretty much the very same.
People must be alarmed, both as customers and as residents. Today, what we care about is really reliant on what is in the news at the minute, and right now security is not in the news. It was not an issue in the 2016 election, and by and large isn’t something that legislators are willing to make a stand on. Snowden informed his story, Congress passed a brand-new law in response, and individuals proceeded.
Surveillance is business model of the web. Everyone is under consistent surveillance by many companies, varying from social networks like Facebook to cellphone suppliers. This information is gathered, compiled, evaluated, and utilized to try to offer us stuff. Individualized advertising is how these business make money, and is why so much of the internet is free to users. It’s a concern of just how much control we allow in our society. Now, the answer is essentially anything goes. It wasn’t constantly this way. In the 1970s, Congress passed a law to make a specific kind of subliminal advertising unlawful since it was thought to be morally wrong. That advertising technique is child’s play compared to the kind of personalized adjustment that business do today. The legal concern is whether cyber-manipulation is a unreasonable and misleading organization practice, and, if so, can the Federal Trade Commission step in and restrict a great deal of these practices.
We’re residing in a world of low federal government effectiveness, and there the dominating neo-liberal concept is that companies must be complimentary to do what they desire. Our system is optimized for business that do whatever that is legal to take full advantage of earnings, with little nod to morality. It’s extremely rewarding, and it feeds off the natural residential or commercial property of computers to produce information about what they are doing. For instance, cellphones require to know where everybody is so they can provide telephone call. As a result, they are ubiquitous security gadgets beyond the wildest dreams of Cold War East Germany.
In basic, Americans tend to skepticism federal government and trust corporations. Europeans tend to trust government and mistrust corporations. The outcome is that there are more controls over federal government security in the U.S. than in Europe.
It seems that U.S. consumers are resigned to the concept of giving up their privacy in exchange for using Google and Facebook for totally free. Customers are worried about their privacy and do not like business understanding their intimate tricks. This is why we need the federal government to step in.
In basic, security professionals aren’t paranoid; they just have a much better understanding of the compromises. Like everybody else, they routinely offer up privacy for convenience. Website or blog registration is an annoyance to the majority of people.
What else can you do to safeguard your privacy online? Many individuals have come to the conclusion that e-mail is fundamentally unsecurable. If I want to have a protected online discussion, I use an encrypted chat application like Signal.
We live in a world where many of our information is out of our control. It’s in the cloud, saved by companies that might not have our benefits at heart. So, while there are technical strategies people can use to secure their privacy, they’re primarily around the edges. The very best suggestion I have for individuals is to get associated with the political process. The very best thing we can do as customers and residents is to make this a political problem. Force our legislators to change the guidelines.
 Opting out doesn’t work. It’s rubbish to tell people not to bring a credit card or not to have an email address. And “buyer beware” is putting too much onus on the person. People do not check their food for pathogens or their airlines for safety. The federal government does it. The government has actually stopped working in securing consumers from internet business and social media giants. This will come around. The only effective method to control big corporations is through huge government. My hope is that technologists also get involved in the political process– in federal government, in think-tanks, universities, and so on. That’s where the genuine change will occur. I tend to be short-term pessimistic and long-lasting optimistic. I do not believe this will do society in. This is not the very first time we’ve seen technological modifications that threaten to undermine society, and it will not be the last.
Opting out doesn’t work. It’s rubbish to tell people not to bring a credit card or not to have an email address. And “buyer beware” is putting too much onus on the person. People do not check their food for pathogens or their airlines for safety. The federal government does it. The government has actually stopped working in securing consumers from internet business and social media giants. This will come around. The only effective method to control big corporations is through huge government. My hope is that technologists also get involved in the political process– in federal government, in think-tanks, universities, and so on. That’s where the genuine change will occur. I tend to be short-term pessimistic and long-lasting optimistic. I do not believe this will do society in. This is not the very first time we’ve seen technological modifications that threaten to undermine society, and it will not be the last.
If you have any questions relating to where by and how to use fake indiana drivers license, you can speak to us at our own internet site.
Fictitious names are presumed names, pseudonyms aside from their for an entity or person. Some states mandate businesses file fictitious names to expose who owns and runs their businesses. designations
Some business owners go with fictitious names to appeal to specific markets or signal professionalism, status and design; others are needed by law to do so.
As part of starting your own business, it is important to comprehend whether filing for DBA in your state is needed prior to beginning operations. Skipping this action might lead to fines or prevent your ability to enforce agreements. At Nav, they use resources to assist with this step if applicable along with finding service credit cards to money its development if needed. Find out more today about what services and items we can use you!
If you have experienced unexpected charges on your bank, charge card, or other monetary accounts without permission, it could be the result of identity theft. Crooks use your personal information to open charge card, loans and even submit fraudulent tax returns in your name; creditors might even send notices that an identity thief has filed suit against you; while cyber attacks such as “phishing” happen when crooks send out emails that look legitimate and request account information (passwords and so on).
Companies utilizing fictitious names should file what’s known as a “fictitious name declaration.” This permits consumers to call them if problems develop with business and its ownership, while lots of online users utilize pseudonyms in order to keep their identity private, such as utilizing an ID instead of their real name when signing onto websites or socials media.
Privacy in today’s digital world is an issue worth facing, with individuals needing to safeguard their individual information such as name and address from cyber-criminals and stalkers. One effective approach for doing this is utilizing pseudonyms online – these permit users to engage without revealing their genuine names to others.
Fictitious names offer an efficient means of circumventing legal name requirements when conducting service activities, for example by sole owners and partnerships when announcing their company or requesting credit. Fictitious names might likewise help services re-brand or go into new markets more quickly while corporate filing can permit multiple restaurants, stores or websites with various brand names under one umbrella name without needing to establish different legal entities for each. Many individuals realize that, in some cases it might be needed to sign up on web sites with make-believe detailed information and many individuals may wish to think about poland fake Id..
A fictitious name can likewise make building organization credit or acquiring service charge card simpler. A lot of states allow services registered under their DBA name to request credit under it when registered; it’s essential to talk to your state department to comprehend what its procedure appears like in your area; some need renewing registration every so often or making necessary updates prior to the expiration date or registration changes, which will keep them certified and prevent their business from falling out of excellent standing with state policies.
Fictitious names been available in different forms; from marketing mottos that capture consumers’ creativity to moniker that signify status or design. Fictitious names should likewise be signed up with their state of operation to prevent legal issues for companies operating under one. Unique and creative names for their companies will help business owners to prevent this commitment and reduce legal issues on their own and their clients alike.
Susan Jones might call her catering company “Catering Capers,” but to secure her legal rights she should file a fictitious name statement connecting that brand name with Smith Enterprises as her legal organization name. If there are problems or require to bring match against it, this provides consumers with access to more details regarding who owns it.
 Entrepreneur ought to also consider utilizing fictitious names when obtaining charge card for their companies. Fictitious names can assist accelerate constructing your credit quicker as lenders view it as separate from personal credit. It is advisable to check with the state department concerning the length of time DBA or fictitious name registration will stay valid as it needs to be restored regularly and some states also require that you identify what kind of entity operates under it when registering your name.
Entrepreneur ought to also consider utilizing fictitious names when obtaining charge card for their companies. Fictitious names can assist accelerate constructing your credit quicker as lenders view it as separate from personal credit. It is advisable to check with the state department concerning the length of time DBA or fictitious name registration will stay valid as it needs to be restored regularly and some states also require that you identify what kind of entity operates under it when registering your name.
Recently a well known Cyber security specialist recently talked with a worried, individual privacy supporter about what consumers can do to safeguard themselves from government and corporate surveillance. Since throughout the current web age, customers appear significantly resigned to giving up basic aspects of their privacy for benefit in using their computers and phones, and have actually grudgingly accepted that being monitored by corporations and even federal governments is simply a truth of contemporary life.
In fact, internet users in the United States have fewer privacy protections than those in other countries. In April, Congress voted to permit internet service providers to gather and offer their customers’ searching information. By contrast, the European Union hit Google this summer with a $3.2 billion antitrust fine.
They talked about federal government and corporate surveillance, and about what worried users can do to protect their privacy. After whistleblower Edward Snowden’s discoveries concerning the National Security Agency’s (NSA) mass surveillance operation in 2013, just how much has the federal government landscape in this field altered?
Snowden’s revelations made people familiar with what was happening, however little bit changed as a result. The USA Freedom Act resulted in some minor changes in one particular federal government data-collection program. The NSA’s information collection hasn’t altered; the laws restricting what the NSA can do have not altered; the technology that permits them to do it hasn’t altered. It’s pretty much the very same.
Individuals need to be alarmed, both as consumers and as citizens. Today, what we care about is very dependent on what is in the news at the moment, and right now surveillance is not in the news. It was not an issue in the 2016 election, and by and large isn’t something that lawmakers want to make a stand on. Snowden informed his story, Congress passed a new law in action, and people carried on.
Surveillance is the business design of the web. Everybody is under consistent surveillance by lots of companies, ranging from social media networks like Facebook to cellphone service providers. This information is gathered, assembled, evaluated, and used to attempt to offer us stuff. Customized marketing is how these business earn money, and is why a lot of the internet is free to users. It’s a question of how much adjustment we allow our society. Now, the response is generally anything goes. It wasn’t constantly this way. In the 1970s, Congress passed a law to make a particular form of subliminal advertising prohibited since it was believed to be morally wrong. That advertising method is child’s play compared to the sort of tailored adjustment that companies do today. The legal question is whether cyber-manipulation is a unfair and misleading company practice, and, if so, can the Federal Trade Commission step in and restrict a great deal of these practices.
We’re living in a world of low government efficiency, and there the dominating neo-liberal idea is that business should be totally free to do what they want. Our system is optimized for companies that do whatever that is legal to make the most of earnings, with little nod to morality. It’s extremely lucrative, and it feeds off the natural property of computer systems to produce data about what they are doing. Cellular phones need to understand where everybody is so they can provide phone calls. As a result, they are common monitoring gadgets beyond the wildest dreams of Cold War East Germany.
Europe has more strict privacy regulations than the United States. In general, Americans tend to mistrust federal government and trust corporations. Europeans tend to rely on federal government and skepticism corporations. The outcome is that there are more controls over government monitoring in the U.S. than in Europe. On the other hand, Europe constrains its corporations to a much higher degree than the U.S. does. U.S. law has a hands-off method of treating internet companies. Electronic systems, for example, are exempt from many normal product-liability laws. This was initially done out of the worry of stifling innovation.
It appears that U.S. clients are resigned to the idea of providing up their privacy in exchange for using Google and Facebook for complimentary. Consumers are concerned about their privacy and don’t like business understanding their intimate tricks. This is why we require the federal government to step in.
In general, security experts aren’t paranoid; they just have a better understanding of the compromises. Like everyone else, they regularly quit privacy for benefit. They just do it intentionally and purposely. Website or blog registration is an annoyance to the majority of people. That’s not the worst aspect of it. You’re generally increasing the risk of having your info stolen. However, sometimes it might be needed to sign up on sites with assumed identification or you might prefer to consider west virginia Fake drivers license..!
What else can you do to safeguard your privacy online? Lots of people have come to the conclusion that e-mail is essentially unsecurable. If I need to have a protected online discussion, I use an encrypted chat application like Signal.
While there are technical methods individuals can employ to secure their privacy, they’re mainly around the edges. The best suggestion I have for people is to get included in the political process. The finest thing we can do as citizens and customers is to make this a political issue.
The government has failed in securing consumers from internet business and social media giants. The only effective method to control huge corporations is through big federal government. My hope is that technologists likewise get included in the political process– in federal government, in think-tanks, universities, and so on.
Because every time you click from one site to another, you click on a web link to go to the following web page– that is data that individuals are gathering about you. That kind of info that you may believe is useless, is the power that powers a great deal of business models.
The initial step is really for people to recognize the purchase that they make when they get something new as well as glossy, that’s complimentary. When you sign up for a brand-new account at whatever solution, checked out the terms of solution at the very least as a lot as you can. What is it that you’re surrendering? Could you give me an instance, like suppose I enroll in a photo-sharing website? Well, congratulations, those photos are now possessed by that company and they can be made use of in marketing efforts, even if those are photos of you and also your family.
If you’re not okay or if you want to regulate when they obtain data and also when they do not, there are a number of web browser expansions like Disconnect and Ghostery. All these web browser extensions provide you manage over whether or not the websites that you visit gather details regarding you and send them to various other relevant companies.
My details is extremely essential and also I’m going to safeguard it as best as I can. As a result, firms all over are producing big storehouses of information on all of us. The most noticeable details being gathered is social media data.
Some groups are also deep profiling your character to specifically adjust their communication with you. The gathering and storage space of this data is becoming one of one of the most profitable enterprises on earth. Whatever you upload, tweet about, like, and also more is being gathered. Also the place from where you publish can be collected, and also can be tracked in real-time, placing you in jeopardy. Even after social media profile accounts are deleted, personal information can still be gathered through a variety of methods. Is claimed and also done, it is crucial to know what is being done with your information, and to make enlightened decisions on what you upload. You don’t need to stop tweeting, you do not need to desert social networks, just ask yourself important questions prior to you publish points on the web.
Are you cool with that info being looked at by any individual on the world wide web? Are you alright with that info being used to profile who you are on the web? Some people understand that, often it may be needed to register on websites with concocted details and many individuals might wish to consider Fake id alaska.
Customized identification cards provide your organization with an extraordinary identification that individuals will certainly keep in mind. Easy to transfer and also look fantastic, novelty identification cards supply a pleasurable method to identify characters in a crowd.
 Novelty ID cards can be an amusing way to bring laughter right into the workplace and have exciting with good friends. While novelty IDs can not be utilized to phony genuine Identifications, they can serve numerous purposes.
Novelty ID cards can be an amusing way to bring laughter right into the workplace and have exciting with good friends. While novelty IDs can not be utilized to phony genuine Identifications, they can serve numerous purposes.
Many teens are getting in pubs as well as clubs with concocted Identifications that look extremely realistic, full with holograms, universal product code, and also various other forms of determining info. Usually these novelty junk IDs can be purchased from sites specializing in novelty product.
Novelty IDs use more customization than regular identification cards; you can make it stand out by using vivid products and also photo-realistic photos, along with bright colors. Novelty IDs allow you to incorporate individual design concepts a lot more easily than conventional ones; you can easily transform message using cloning devices while being conscious of its design when making these distinct identification cards.
Novelty ID cards are a very easy and entertaining way to share information concerning yourself with others. Not just are they hassle-free, however they’re great for standing out among a group or perhaps playing jokes on good friends – make certain that any usabilities for such Identifications are ideal as well as not meant for prohibited activities!
Layout of an ID card is an indispensable variable of its performance. You need to pick a theme that matches with the kind of Identification you plan to design, whether that includes pictures or just ordinary text-based aspects.
Net searches will certainly generate numerous California sham id themes, designed to look reasonable and also also deceive law enforcement officer. Some also include holograms and barcodes the same to those seen on actual state-issued recognition papers. Some individuals realize that, sometimes it may be very necessary to register on web sites with fictitious detailed information and many people may want to consider fake id slovenia..
Novelty identification cards are an engaging way to add personality and also panache to your identity. By damaging out of the mold, these one-of-a-kind identification cards allow you to believe outside package and get individuals’s interest in interesting as well as brand-new ways. Not just are novelty ID cards excellent methods of revealing off creative thinking or advertising brands yet they are likewise an optimal gift suggestion!
Lots of people can make fabricating an individualized ID card basic with AI technology. Select from a variety of templates, submit your very own image, customize message as well as more; explore different fonts, colors as well as dimensions – plus our intuitive full-screen editor helps craft catchy headings as well as significant messages!
Identification cards give members of a group or organization with true subscription status and also recognition, assisting occasion personnel quickly determine members. Novelty IDs may also be used for amusing pranks against coworkers and good friends; however, novelty ids must never ever be utilized unlawfully.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, de-laminação e des-metalização e desbotamento precoce. Essa garantia não se aplica a defeitos na instalação, e manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto deverá ser feita com nota fiscal eletrônica de devolução com as características iguais a nota de venda. A garantia será feita somente no valor e quantidade dos produtos adquiridos, não sendo devolvido valores em espécie, somente em produtos e não contemplando a mão de obra de instalação.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto acompanhado de sua respectiva nota fiscal, modelo e transparência do material.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, delaminação e des-metalização, de materiais instalados conforme suas especificações e utilidades.
Esta garantia não se aplica a defeitos na instalação, bem como manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto instalado, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto para garantia deverá ser feita com nota fiscal eletrônica (emitida pela loja instaladora), com as características iguais a nota de venda.
A garantia será feita somente no valor e quantidade dos produtos adquiridos, não permeando valores de mão de obra de aplicação, e posteriormente o produto será encaminhado ao instalador para substituição.
