Cyber hazards come from lots of sources, each looking to acquire personal information (PI) for benefit or exploitation. Internet privacy is a subset of the larger world of information privacy that covers the collection, usage, and safe storage of PI usually.
A Pew Research Institute research study discovered that controlling PI on line is “extremely crucial” to 72% of Americans. According to another Pew research study, 77% of Americans have done something about it to preserve their privacy– erasing cookies, securing e-mail, and securing their IP address.
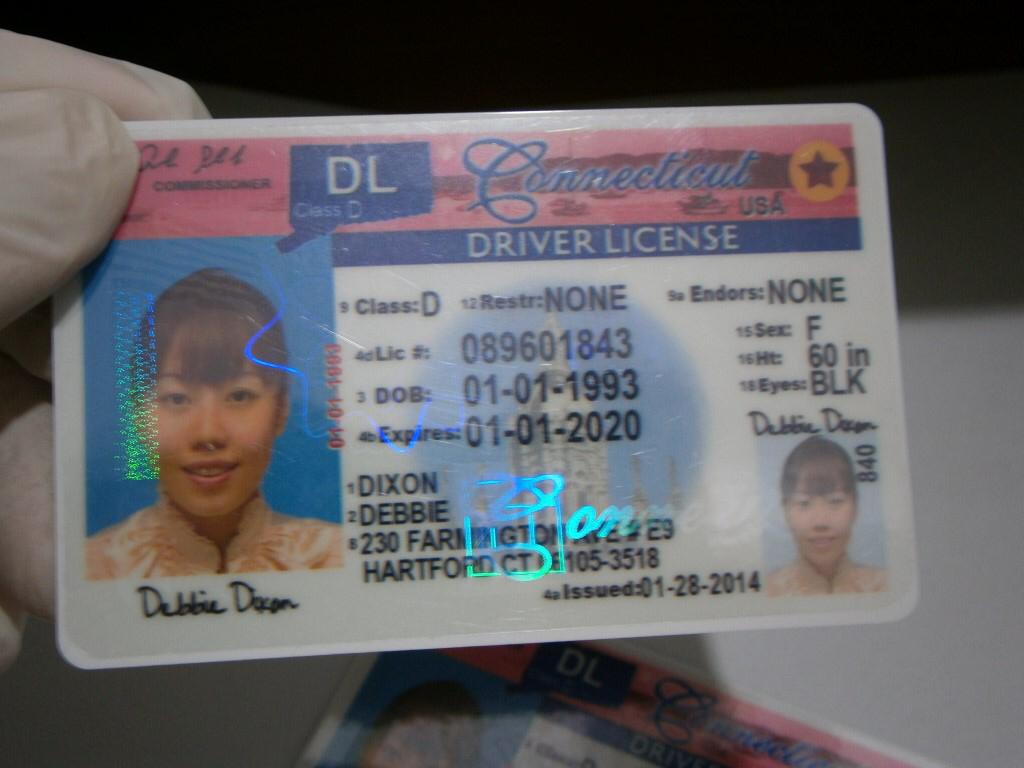
Digital footprints are all over. Each time you visit an internet site, enter your credit or debit card info, register for an account, provide your email, submit online kinds, post on social media, or store images or documents in cloud storage, you are launching personal information into cyberspace. Just who, aside from the desired recipient, will have or get access to the details you supplied? Will it be shown other celebrations? Your PI may be shared in ways you do not expect or are unaware of. Your info may be at some danger since even the best details security programs are not 100% ensured. Site registration is an annoyance to most people. That’s not the worst aspect of it. You’re generally increasing the risk of having your info taken. But, often it may be needed to sign up on sites with make-believe identity or you may wish to consider fake Indiana Drivers license !
There is no single law controling online privacy. Some key federal laws affecting online privacy include:
The Federal Trade Commission Act (FTC) [1914]– manages deceptive or unreasonable industrial practices. The FTC is the main federal regulator in the privacy area and brings enforcement actions versus companies. This consists of failing to abide by published privacy policies and stopping working to sufficiently safeguard individual details.
Electronic Communications Privacy Act (ECPA) [1986] – secures specific wire, oral, and electronic interactions from unauthorized interception, disclosure, access, and use.
— makes illegal certain computer-related activities involving the unapproved gain access to of a computer to acquire certain info, get or defraud anything of worth, transmit harmful items, or traffic in computer passwords.
Kid’s Online Privacy Protection Act (COPPA) [1998]– needs particular site and online service providers to obtain proven adult permission before gathering, using, or revealing personal info from minors under the age of 13. It likewise requires web sites to post an online privacy policy, gather only the personal details needed, and develop and keep affordable security measures.
Controlling the Assault of Non-Solicited Pornography and Marketing Act (CAN-SPAM Act) [2003]— governs sending out unsolicited industrial email and forbids deceptive header info and misleading subject lines. It likewise requires senders to reveal specific information, consist of a legitimate opt-out mechanism, and it creates criminal and civil penalties for offenses.
Financial Services Modernization Act (GLBA) [1999]– controls the collection, usage, and disclosure of personal info collected or held by financial institutions and needs consumer notices and a composed details security program.
Fair and Accurate Credit Transactions Act (FACTA) [2003]– needs financial institutions and financial institutions to maintain written identity theft avoidance programs.
Lots of states have also embraced laws impacting online privacy, for instance, consumer protection statutes, laws that safeguard specific classifications of PI, info security laws, and data breach alert laws. In addition to adhering to these laws and executing robust details security programs, there are actions organizations can take to help reduce cybersecurity risks.
Client, customer, and staff member personal info in your ownership can be based on a data breach in a myriad of ways. E-mail addresses, banking, passwords, physical addresses, contact number and more can inadvertently discover their methods to scammers, hackers, undesired online marketers, and more. The majority of compliance and legal location employees have little idea how to go carry out information defense from web hazards. Quite a few individuals realize that, often it might be very necessary to register on websites with invented specifics and many people may wish to consider Colorado Fake Drivers License..!
 Something your company can do is establish an Internet privacy quick reference playbook that is quickly available to workers. It can offer details and best practices to follow for your particular location.
Something your company can do is establish an Internet privacy quick reference playbook that is quickly available to workers. It can offer details and best practices to follow for your particular location.
Don’t count on your browser’s default settings, whenever you use your computer, but rather re-set its privacy settings to maximize your privacy.
Content and advertisement stopping tools take a heavy technique, suppressing whole areas of a site’s law to prevent widgets and other law from operating and some site modules (usually advertisements) from displaying, which likewise reduces any trackers embedded in them. Advertisement blockers attempt to target ads specifically, whereas material blockers look for JavaScript and other modules that may be unwelcome.
Because these blocker tools maim parts of sites based on what their developers believe are signs of unwelcome site behaviours, they frequently harm the performance of the website you are trying to utilize. Some are more surgical than others, so the outcomes vary commonly. If a website isn’t running as you anticipate, attempt putting the site on your internet browser’s “enable” list or disabling the content blocker for that site in your browser.
I’ve long been sceptical of material and ad blockers, not just since they kill the revenue that legitimate publishers need to remain in service however also due to the fact that extortion is business design for numerous: These services frequently charge a cost to publishers to permit their ads to go through, and they block those ads if a publisher does not pay them. They promote themselves as helping user privacy, however it’s barely in your privacy interest to just see advertisements that paid to make it through.
Naturally, deceitful and desperate publishers let ads get to the point where users wanted ad blockers in the first place, so it’s a cesspool all around. However modern browsers like Safari, Chrome, and Firefox significantly block “bad” ads (nevertheless defined, and generally rather minimal) without that extortion organization in the background.
Firefox has actually recently surpassed blocking bad advertisements to featuring stricter content blocking options, more akin to what extensions have long done. What you really desire is tracker blocking, which nowadays is managed by numerous internet browsers themselves or with the help of an anti-tracking extension.
Mobile browsers normally feature fewer privacy settings despite the fact that they do the same basic spying on you as their desktop siblings do. Still, you need to utilize the privacy controls they do offer. Is signing up on internet sites dangerous? I am asking this question since just recently, several sites are getting hacked with users’ passwords and emails were possibly stolen. And all things considered, it may be essential to sign up on website or blogs using pseudo details and some people may wish to think about minnesota Fake drivers license!
In terms of privacy abilities, Android and iOS internet browsers have actually diverged in the last few years. All web browsers in iOS use a typical core based on Apple’s Safari, whereas all Android internet browsers utilize their own core (as is the case in Windows and macOS). That suggests iOS both standardizes and restricts some privacy features. That is likewise why Safari’s privacy settings are all in the Settings app, and the other internet browsers manage cross-site tracking privacy in the Settings app and carry out other privacy functions in the browser itself.
Here’s how I rank the mainstream iOS web browsers in order of privacy assistance, from many to least– presuming you use their privacy settings to the max.
And here’s how I rank the mainstream Android internet browsers in order of privacy support, from most to least– likewise presuming you use their privacy settings to the max.
The following 2 tables show the privacy settings offered in the major iOS and Android browsers, respectively, as of September 20, 2022 (variation numbers aren’t frequently revealed for mobile apps). Controls over microphone, place, and electronic camera privacy are managed by the mobile operating system, so utilize the Settings app in iOS or Android for these. Some Android internet browsers apps supply these controls straight on a per-site basis as well. Your personal data is precious and in some cases it might be necessary to sign up on sites with concocted information, and you may desire to consider fake canada nova scotia drivers license!. Some websites want your e-mail addresses and individual information so they can send you advertising and make money from it.
A couple of years ago, when ad blockers became a popular way to combat abusive sites, there came a set of alternative browsers indicated to strongly protect user privacy, interesting the paranoid. Brave Browser and Epic Privacy Browser are the most popular of the new breed of browsers. An older privacy-oriented web browser is Tor Browser; it was developed in 2008 by the Tor Project, a non-profit founded on the concept that “internet users need to have personal access to an uncensored web.”
All these web browsers take a highly aggressive approach of excising entire pieces of the websites law to prevent all sorts of functionality from operating, not just advertisements. They typically block features to sign up for or sign into internet sites, social media plug-ins, and JavaScripts simply in case they may collect personal information.
Today, you can get strong privacy security from mainstream browsers, so the requirement for Brave, Epic, and Tor is rather small. Even their most significant claim to fame– obstructing ads and other frustrating content– is progressively managed in mainstream internet browsers.
One alterative internet browser, Brave, appears to use ad blocking not for user privacy defense however to take incomes far from publishers. Brave has its own advertisement network and desires publishers to utilize that instead of contending ad networks like Google AdSense or Yahoo Media.net. It tries to require them to utilize its ad service to reach users who select the Brave internet browser. That feels like racketeering to me; it ‘d resemble informing a shop that if people wish to patronize a specific credit card that the store can offer them just products that the credit card company provided.
Brave Browser can reduce social networks integrations on web sites, so you can’t use plug-ins from Facebook, Twitter, LinkedIn, Instagram, and so on. The social media companies collect substantial quantities of individual information from people who use those services on websites. Do note that Brave does not honor Do Not Track settings at sites, treating all sites as if they track ads.
The Epic web browser’s privacy controls resemble Firefox’s, but under the hood it does one thing very differently: It keeps you far from Google servers, so your details doesn’t take a trip to Google for its collection. Numerous internet browsers (particularly Chrome-based Chromium ones) use Google servers by default, so you don’t recognize just how much Google in fact is associated with your web activities. However if you sign into a Google account through a service like Google Search or Gmail, Epic can’t stop Google from tracking you in the browser.
Epic likewise provides a proxy server implied to keep your web traffic away from your internet service provider’s data collection; the 1.1.1.1 service from CloudFlare provides a comparable center for any browser, as described later.
Tor Browser is a vital tool for reporters, whistleblowers, and activists likely to be targeted by corporations and federal governments, in addition to for individuals in countries that monitor the web or censor. It utilizes the Tor network to conceal you and your activities from such entities. It also lets you publish internet sites called onions that require extremely authenticated access, for extremely private details distribution.
There is some bad news and great trending news about web based privacy. I spent recently reviewing the 53,000 words of data privacy terms released by eBay and Amazon, attempting to extract some straight answers, and comparing them to the privacy regards to other web based marketplaces.
The bad news is that none of the privacy terms analysed are excellent. Based upon their released policies, there is no major online market operating in the United States that sets a commendable standard for respecting customers information privacy.
All the policies include vague, confusing terms and offer customers no real option about how their data are collected, utilized and divulged when they shop on these websites. Online merchants that operate in both the United States and the European Union offer their consumers in the EU better privacy terms and defaults than us, because the EU has stronger privacy laws.
The United States customer supporter groups are currently collecting submissions as part of a questions into online marketplaces in the United States. The bright side is that, as a first step, there is a clear and basic anti-spying guideline we could present to eliminate one unjust and unnecessary, however extremely typical, data practice. Deep in the fine print of the privacy regards to all the above called online sites, you’ll discover a disturbing term. It says these sellers can obtain additional data about you from other business, for example, data brokers, marketing business, or providers from whom you have previously acquired.
Some big online seller online sites, for instance, can take the data about you from a data broker and integrate it with the information they currently have about you, to form a detailed profile of your interests, purchases, behaviour and characteristics. Some people realize that, sometimes it might be essential to register on online sites with false information and many individuals might wish to consider fake vermont drivers license.
The problem is that online markets provide you no choice in this. There’s no privacy setting that lets you pull out of this data collection, and you can’t get away by switching to another major marketplace, due to the fact that they all do it. An online bookseller does not need to collect information about your fast-food preferences to sell you a book. It wants these additional data for its own marketing and business functions.
You may well be comfortable providing merchants info about yourself, so as to receive targeted ads and help the retailer’s other service purposes. But this preference must not be presumed. If you desire merchants to collect data about you from 3rd parties, it needs to be done just on your explicit guidelines, rather than automatically for everyone.
The “bundling” of these uses of a consumer’s data is potentially unlawful even under our existing privacy laws, but this requires to be explained. Here’s a tip, which forms the basis of privacy advocates online privacy query. Online retailers ought to be barred from collecting data about a customer from another company, unless the customer has plainly and actively requested this.
For instance, this might involve clicking on a check-box beside a plainly worded guideline such as please acquire details about my interests, requirements, behaviours and/or qualities from the following information brokers, advertising business and/or other suppliers.
The 3rd parties must be specifically named. And the default setting should be that third-party data is not collected without the consumer’s reveal request. This guideline would be consistent with what we know from customer surveys: most consumers are not comfy with companies unnecessarily sharing their personal details.
There could be sensible exceptions to this rule, such as for scams detection, address verification or credit checks. But information acquired for these functions need to not be utilized for marketing, advertising or generalised “market research”. Online markets do claim to allow choices about “customised marketing” or marketing interactions. Sadly, these are worth little in terms of privacy defense.
Amazon states you can pull out of seeing targeted marketing. It does not state you can pull out of all data collection for advertising and marketing purposes.
Similarly, eBay lets you pull out of being revealed targeted ads. The later passages of its Cookie Notice state that your data may still be collected as explained in the User Privacy Notice. This offers eBay the right to continue to gather information about you from information brokers, and to share them with a variety of third parties.
Many retailers and large digital platforms operating in the United States justify their collection of consumer data from 3rd parties on the basis you’ve already given your indicated grant the 3rd parties revealing it.
That is, there’s some odd term buried in the thousands of words of privacy policies that apparently apply to you, which states that a business, for example, can share data about you with various “associated business”.
Obviously, they didn’t highlight this term, not to mention offer you an option in the matter, when you purchased your hedge cutter last year. It only consisted of a “Policies” link at the foot of its online site; the term was on another websites, buried in the details of its Privacy Policy.
Such terms ought to ideally be eradicated totally. However in the meantime, we can turn the tap off on this unjust flow of data, by stating that online sellers can not acquire such data about you from a third party without your express, indisputable and active request.
Who should be bound by an ‘anti-spying’ rule? While the focus of this short article is on online marketplaces covered by the customer supporter inquiry, numerous other business have similar third-party data collection terms, including Woolworths, Coles, significant banks, and digital platforms such as Google and Facebook.
 While some argue users of “complimentary” services like Google and Facebook should anticipate some monitoring as part of the deal, this must not encompass asking other business about you without your active permission. The anti-spying rule ought to plainly apply to any web site selling a product and services.
While some argue users of “complimentary” services like Google and Facebook should anticipate some monitoring as part of the deal, this must not encompass asking other business about you without your active permission. The anti-spying rule ought to plainly apply to any web site selling a product and services.
Six months ago privacy data consumer advocates announced proposed upcoming legislation to establish an online privacy law setting tougher privacy requirements for Facebook, Google, Amazon and lots of other online platforms. These businesses gather and use vast amounts of customers individual information, much of it without their knowledge or real permission, and the law is intended to guard against privacy damages from these practices.
 The higher requirements would be backed by increased penalties for disturbance with privacy under the Privacy Act and greater enforcement powers for the federal privacy commissioner. Major or duplicated breaches of the law might bring penalties for business.
The higher requirements would be backed by increased penalties for disturbance with privacy under the Privacy Act and greater enforcement powers for the federal privacy commissioner. Major or duplicated breaches of the law might bring penalties for business.

Nevertheless, relevant business are likely to attempt to prevent obligations under the law by drawing out the procedure for signing up the law and drafting. They are likewise likely to attempt to exclude themselves from the code’s coverage, and argue about the meaning of personal information.
The present meaning of individual details under the Privacy Act does not clearly consist of technical information such as IP addresses and gadget identifiers. Updating this will be crucial to guarantee the law is effective.
The law would target online platforms that “gather a high volume of personal information or trade in individual info”, consisting of social networks networks such as Facebook; dating apps like Bumble; online blogging or online forum websites like Reddit; video gaming platforms; online messaging and video conferencing services such as WhatsApp, Zoom and data brokers that sell individual information as well as other big online platforms that collect personal details.
The law would impose higher standards for these business than otherwise apply under the Privacy Act. The law would likewise set out information about how these organisations must fulfill obligations under the Privacy Act. This would consist of greater standards for what constitutes users consent for how their data is utilized.
The government’s explanatory paper states the law would require approval to be voluntary, notified, unambiguous, specific and current. The draft legislation itself does not really state that, and will require some modification to achieve this.
This description makes use of the definition of consent in the General Data Protection Regulation. Under the proposed law, customers would have to give voluntary, informed, unambiguous, existing and particular consent to what business do with their information.
In the EU, for example, unambiguous consent indicates a person needs to take clear, affirmative action– for example by ticking a box or clicking a button– to consent to a use of their information. Approval should likewise be specific, so business can not, for instance, require customers to grant unassociated usages such as marketing research when their information is only required to process a specific purchase.
The consumer supporter suggested we need to have a right to erase our personal information as a means of lowering the power imbalance in between consumers and large platforms. In the EU, the “right to be forgotten” by search engines and the like is part of this erasure. The federal government has not adopted this recommendation.
The law would include a commitment for organisations to comply with a customer’s reasonable demand to stop using and disclosing their personal data. Companies would be enabled to charge a non-excessive charge for satisfying these requests. This is an extremely weak version of the EU right to be forgotten.
For instance, Amazon currently specifies in its privacy policy that it utilizes consumers individual information in its advertising service and discloses the information to its large Amazon.com corporate group. The proposed law would mean Amazon would have to stop this, at a consumers request, unless it had sensible grounds for refusing.
Ideally, the law ought to likewise enable customers to ask a company to stop gathering their individual details from third parties, as they presently do, to construct profiles on us.
The draft bill also includes an unclear arrangement for the law to include securities for kids and other susceptible individuals who are not capable of making their own privacy decisions.
A more questionable proposition would require brand-new approvals and verification for kids utilizing social networks services such as Facebook and WhatsApp. These services would be required to take affordable steps to confirm the age of social media users and obtain adult consent prior to collecting, using or divulging individual information of a kid under 16 of age.
A key tactic business will likely use to avoid the new laws is to declare that the information they utilize is not truly personal, considering that the law and the Privacy Act only apply to personal details, as defined in the law. Some individuals recognize that, in some cases it may be very necessary to register on sites with fictitious specifics and many people may wish to think about Fake Ohio Drivers License.!
The companies may declare the data they collect is just linked to our private gadget or to an online identifier they’ve designated to us, instead of our legal name. The result is the same. The information is utilized to develop a more comprehensive profile on a specific and to have effects on that person.
The United States, needs to update the definition of personal information to clarify it consisting of data such as IP addresses, device identifiers, location information, and any other online identifiers that might be utilized to determine a specific or to communicate with them on a private basis. If no person is identifiable from that information, data must just be de-identified.
The federal government has vowed to provide tougher powers to the privacy commissioner, and to hit business with harder penalties for breaching their obligations as soon as the law enters effect. The optimum civil charge for a repetitive and/or serious disturbance with privacy will be increased approximately the comparable penalties in the Consumer security Law.
For people, the optimum charge will increase to more than $500,000. For corporations, the optimum will be the higher of $10 million, or 3 times the value of the benefit gotten from the breach, or if this worth can not be figured out 12% of the company’s yearly turnover.
The privacy commission might likewise issue violation notifications for failing to supply appropriate information to an investigation. Such civil penalties will make it unneeded for the Commission to resort to prosecution of a criminal offence, or to civil litigation, in these cases.
The tech giants will have plenty of chance to create hold-up in this process. Companies are likely to challenge the material of the law, and whether they ought to even be covered by it at all.
The Internet data security and privacy laws control how a person’s personal information is collected, handled, used, processed and shared. The law also limits what details is openly available, and it can enable withholding of particular info that could be harmful
 HIPAA is one of the most considerable pieces of data privacy legislation in the U.S. This is a significant law that avoids your safeguarded health details (PHI) from being shared by a medical institution without your approval. The FTC likewise mandates information breach notifications, so if a medical company has suffered a data breach, it must immediately inform all of its clients.
HIPAA is one of the most considerable pieces of data privacy legislation in the U.S. This is a significant law that avoids your safeguarded health details (PHI) from being shared by a medical institution without your approval. The FTC likewise mandates information breach notifications, so if a medical company has suffered a data breach, it must immediately inform all of its clients.
It prevents breaches of patient-doctor confidence and prevents a medical institution from sharing client information with collaborators (you require to sign consent for that, also). HIPAA likewise covers any institution or private providing medical services, including psychologists and chiropractics physician.
The guidelines of HIPAA are very strict, and even something as innocuous as your medical professional telling your mom you have a cold, or a nurse going through your case history without consent makes up a breach. If they store any recognizable data (like your date of birth), even mobile health apps and cloud storage services need to comply with HIPAA.
The Family Educational Rights and Privacy Act (FERPA) safeguards the data in a trainee’s academic record and governs how it can be launched, revealed, accessed or changed. It permits parents of underage students to access the educational records of their kids and demand that they be changed if necessary.
The law also restricts what information is publicly available, and it permits trainees and moms and dads of underage students to withhold certain information that might be damaging to the future of a trainee.
FERPA has some overlap with HIPAA and is the cause for the so-called FERPA exception. In cases where an university holds what could be thought about medical data (like information on a counseling session, or on-campus medical treatments), FERPA takes precedence over HIPAA, and its guidelines are followed concerning how that information is handled.
The Children’s Online Privacy Protection Act (COPPA) looks for to secure children under 13 from online predation, and imposes stringent rules on how the information of these children is dealt with. This includes carrying out proven parental approval (kids can not consent to the handling of their information), limiting marketing to children, offering a clear summary of what data gets gathered, and deleting any information that is no longer required.
Because COPPA requirements are extremely stringent, a lot of social media companies just claim to not provide service to kids under 13 to avoid having to comply. This doesn’t prevent those children from just producing an account on their own and sharing potentially harmful personal info online, and the business can simply shift the blame to the parents.
Owing to the lack of adequate defense, parents must take active procedures to protect their children. Restricting access to social media websites via a filtering program is the most convenient way to prevent children from accessing dangerous sites, and some ISPs supply such tools.
U.S. Data Privacy Laws by State … State information security laws are far more progressive compared to federal law. California and Virginia are leading the charge in data protection legislation, however other states are signing up with the fight versus personal data abuse, too. Site registration is an annoyance to most people. That’s not the worst feature of it. You’re essentially increasing the danger of having your info taken. However, in some cases it may be needed to sign up on website or blogs with pretended id or you might wish to think about Missouri Fake Drivers License..!
Like the GDPR, these laws have an extraterritorial reach, in that any business wishing to offer services to residents of an American state needs to abide by its privacy laws. Here are the four state laws presently protecting personal information.
California probably has the very best privacy laws in the United States. The California Consumer Privacy Act (CPA) was a major piece of legislation that passed in 2018, protecting the information privacy of Californians and placing stringent information security requirements on companies.
The CCPA draws lots of contrasts to the European GDPR, which is full marks considering the outstanding information defense the EU manages its citizens. Amongst these parallels is the right of people to gain access to all information a business has on them, as well as the right to be forgotten– or simply put, have your individual information deleted. Nevertheless, most likely the most important similarity between the gdpr and the ccpa is how broadly they both translate the term “personal information.”
Under the CCPA meaning, individual information is any “information that recognizes, associates with, explains, can being associated with or might reasonably be linked, directly or indirectly, with a particular consumer or household.”
This is a landmark meaning that prevents data brokers and advertisers from collecting your individual data and profiling you, or at least makes it very hard for them to do so. The California Privacy Rights Act (CPRA) is another Californian act that changes the CCPA to expand its scope. Most significantly, it developed the California Privacy Protection Agency, in charge of carrying out the laws and making sure they’re followed.
Virginia’s Consumer Data Protection Act (CDPA) bears lots of similarities to the CCPA and GDPR, and is based upon the exact same principles of individual data security. Covered entities have the same responsibilities as under CCPA, consisting of offering users the right to gain access to, view, download and delete individual info from a company’s database.
Covered entities include ones that process the data of a minimum of 100,000 individuals every year, or ones that process the information of at least 25,000 people each year but get at least 40% of their income from selling that data (like information brokers). Virginia’s CDPA differs from the CCPA in the scope of what constitutes the sale of individual info, utilizing a narrower meaning. CCPA and GDPR specify it as the exchange of individual details, either for money or for other reasons, whereas CDPA narrows down those other reasons to simply a couple of particular cases.
Also noteworthy is the absence of a dedicated regulatory authority like the one formed in California under CPRA. The current regulator is Virginia’s attorney general of the United States, which means the law might be harder to impose than it is in California..
Furthermore, Virginia’s CDPA does not consist of a private right of action, suggesting that Virginia residents can not sue business for CDPA violations.
The Colorado Privacy Act (ColoPA) follows in the footsteps of its predecessors and sticks to the very same concepts of personal details protection. There’s actually no noteworthy distinction in between it and California’s guidelines, although it goes a bit further in a few of its protections..
For example, CCPA permits a customer to demand access to all their individual data (utilizing the definition of personal information under CCPA), while ColoPA gives a customer access to information of any kind that a business has on them.
It likewise includes a delicate data requirement to consent requests. This indicates that an information processor need to request special approval to process data that might classify a person into a safeguarded category (such as race, gender, religion and medical diagnoses). At the time of writing, ColoPA is enforced by Colorado’s attorney general.
The Utah Consumer Privacy Act (UCPA) is the current state data security law to be passed in the U.S. Like all the previous laws, it uses the example set by the GDPR, so we’ll just mention what sets it apart.
One significant point of distinction is that its definition of personal data only applies to consumer data. This excludes data that an employer has about its workers, or that a business gets from another organization.
There is also no requirement for information protection assessments. Colorado’s law requires a repeating security audit for all data processors to guarantee they’re implementing sensible information security steps, but Utah enforces no such requirement. There’s also a $35 million yearly earnings limit for information processors– entities making less than that do not require to comply.
The best method to keep your online activity private is to utilize a VPN whenever you’re online A VPN will encrypt your traffic, making it difficult for anybody to understand what online sites you’re checking out. You can take a look at our list of the very best VPNs to discover one that matches your requirements.
Nevertheless, not even a VPN can prevent a website from gathering info about you if you’ve given it any personal information. Utilizing a VPN can’t stop Facebook from seeing what you’ve liked on its site and linking that to your e-mail. This data could then get handed down to data brokers and advertisers.
Regrettably, you can’t know for sure which data brokers have your data. Plus, the only thing you can do to get your data gotten rid of from a data broker’s archive is to ask to do so and hope they follow up.
The Good News Is, Surfshark Incogni– the very best information privacy management tool– is a service to this scenario. The service that acts on your behalf, calling data brokers to get them to eliminate your information.
It does the laborious job of going through each broker in its database and following up numerous times to press them into actually deleting your details. You can read our review of Incogni if you need to know more.
Information privacy laws are key for keeping your details safe. Federal data privacy laws in the U.S. are doing not have in contrast to the data protection efforts of the European Union, but individual states are progressively stepping up to satisfy the privacy needs of their residents.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, de-laminação e des-metalização e desbotamento precoce. Essa garantia não se aplica a defeitos na instalação, e manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto deverá ser feita com nota fiscal eletrônica de devolução com as características iguais a nota de venda. A garantia será feita somente no valor e quantidade dos produtos adquiridos, não sendo devolvido valores em espécie, somente em produtos e não contemplando a mão de obra de instalação.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto acompanhado de sua respectiva nota fiscal, modelo e transparência do material.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, delaminação e des-metalização, de materiais instalados conforme suas especificações e utilidades.
Esta garantia não se aplica a defeitos na instalação, bem como manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto instalado, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto para garantia deverá ser feita com nota fiscal eletrônica (emitida pela loja instaladora), com as características iguais a nota de venda.
A garantia será feita somente no valor e quantidade dos produtos adquiridos, não permeando valores de mão de obra de aplicação, e posteriormente o produto será encaminhado ao instalador para substituição.
