Customized identification cards provide your organization with an extraordinary identification that individuals will certainly keep in mind. Easy to transfer and also look fantastic, novelty identification cards supply a pleasurable method to identify characters in a crowd.
 Novelty ID cards can be an amusing way to bring laughter right into the workplace and have exciting with good friends. While novelty IDs can not be utilized to phony genuine Identifications, they can serve numerous purposes.
Novelty ID cards can be an amusing way to bring laughter right into the workplace and have exciting with good friends. While novelty IDs can not be utilized to phony genuine Identifications, they can serve numerous purposes.
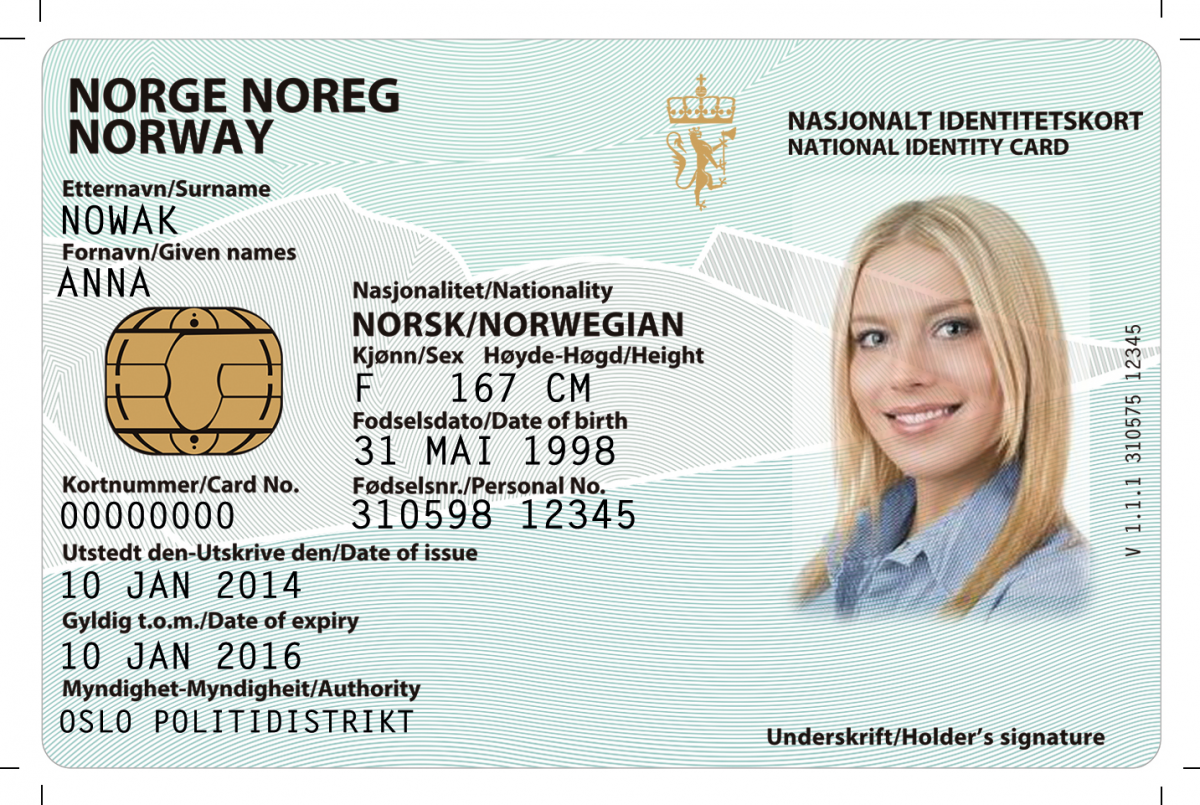
Many teens are getting in pubs as well as clubs with concocted Identifications that look extremely realistic, full with holograms, universal product code, and also various other forms of determining info. Usually these novelty junk IDs can be purchased from sites specializing in novelty product.
Novelty IDs use more customization than regular identification cards; you can make it stand out by using vivid products and also photo-realistic photos, along with bright colors. Novelty IDs allow you to incorporate individual design concepts a lot more easily than conventional ones; you can easily transform message using cloning devices while being conscious of its design when making these distinct identification cards.
Novelty ID cards are a very easy and entertaining way to share information concerning yourself with others. Not just are they hassle-free, however they’re great for standing out among a group or perhaps playing jokes on good friends – make certain that any usabilities for such Identifications are ideal as well as not meant for prohibited activities!
Layout of an ID card is an indispensable variable of its performance. You need to pick a theme that matches with the kind of Identification you plan to design, whether that includes pictures or just ordinary text-based aspects.
Net searches will certainly generate numerous California sham id themes, designed to look reasonable and also also deceive law enforcement officer. Some also include holograms and barcodes the same to those seen on actual state-issued recognition papers. Some individuals realize that, sometimes it may be very necessary to register on web sites with fictitious detailed information and many people may want to consider fake id slovenia..
Novelty identification cards are an engaging way to add personality and also panache to your identity. By damaging out of the mold, these one-of-a-kind identification cards allow you to believe outside package and get individuals’s interest in interesting as well as brand-new ways. Not just are novelty ID cards excellent methods of revealing off creative thinking or advertising brands yet they are likewise an optimal gift suggestion!
Lots of people can make fabricating an individualized ID card basic with AI technology. Select from a variety of templates, submit your very own image, customize message as well as more; explore different fonts, colors as well as dimensions – plus our intuitive full-screen editor helps craft catchy headings as well as significant messages!
Identification cards give members of a group or organization with true subscription status and also recognition, assisting occasion personnel quickly determine members. Novelty IDs may also be used for amusing pranks against coworkers and good friends; however, novelty ids must never ever be utilized unlawfully.
Lots of people want to be safer as well as more private online. The internet has actually become a crucial part of the modern universe. However gathering the data we generate online has come to be the standard for both federal governments and also big technology firms. As well as there are several methods this information about you can be made use of and none of which serve to absolutely help you.
So what in the world can you do about this, given that it’s not reasonable to go live out in the woods alone permanently, well a minimum of for a lot of you anyhow, so for now we have to take actions to reduce these privacy issues any time we can.
We are going to go over several functional steps that we advise to everybody to shield their online digital privacy and protection. Abandoning chrome will certainly go a lengthy means in assisting you redeem your online privacy as well as it takes a lot less than 30 seconds to do, if you want to go above and beyond the regular experience.
For also better privacy you can separate certain internet tasks. Maybe you have a social media sites account where you only log right into accounts like facebook or a work profile where you just gain access to various other accounts. The choices are endless, there are a few various other setups we ‘d invite you to transform such as removing the crypto junk from the residence display as well as disabling various other apps for an also faster and also much more very little net experience.
Altering your default internet search engine to something that does not track you and also hinder your personal privacy helps a lot as well as provides you google search engine result privately. Altering your default online search engine is definitely far better for your privacy than google, but select something that you actually appreciate making use of and also you’ll really have among the most important factors you can do to protect your online digital life. Quite a few people understand that, in some cases it may be needed to register on online sites with invented details and many people may want to consider Canada fake id.!
Shielding your online accounts by mosting likely to the following level with two-factor verification, combines something you understand like a password with something you have, like a code generated on your tool. SMS 2fa, is better than nothing but, it can be prone to sim-swapping assaults. When logging right into accounts, the more secure option is to make use of an application on your phone that generates single passwords to provide a second verification method. This suggests that even if someone does procure your username and password to an account they still will not have the ability to visit without this code, which is constantly altering. Thankfully an increasing number of solutions are providing that, so see to it to utilize it when readily available. Go through all your application services to find out which ones have them.
Individuals can additionally change from a conventional email carrier like gmail or yahoo, if they utilize that, to a solution that uses better privacy. If you utilize ios, imessage is a good alternative as it provides end-to-end encryption by default definition just you and also the recipient can read the messages if you’re on android.
An excellent open source cross-platform messenger referral is Signal, which is an open resource cross-platform carrier signal makes use of end-to-end encryption to protect your texts voice as well as video clip telephone calls and also maintains almost no discreet metadata in the process. It also sustains acquainted functions such as voice recordings sticker labels as well as gifs as well as it even has desktop computer support we strongly advise changing to Signal and also obtaining as lots of people in your life to switch as you can.
 We have more information to share and also we additionally have a comprehensive exactly how to become anonymous overview and also an exactly how to go anonymous guide. For those of you who truly reverberated with this article, we also have tool details overviews, if you want to find out exactly how to upgrade each gadget in your life, up to much better on the internet privacy and also security degrees.
We have more information to share and also we additionally have a comprehensive exactly how to become anonymous overview and also an exactly how to go anonymous guide. For those of you who truly reverberated with this article, we also have tool details overviews, if you want to find out exactly how to upgrade each gadget in your life, up to much better on the internet privacy and also security degrees.
 Lots of people have been busted making use of deceitful identification to purchase alcohol or gain entrance to clubs, with bogus IDs becoming an enhancing issue that might potentially bring about criminal problems if used maliciously.
Lots of people have been busted making use of deceitful identification to purchase alcohol or gain entrance to clubs, with bogus IDs becoming an enhancing issue that might potentially bring about criminal problems if used maliciously.
I. d. documents are very easy to detect by meticulously examining their good quality, utilizing solid components like upped wording, fine lines or microtext as indicators of pseudo Identifications. Additionally, UV and also hologram characteristics need to additionally be explored.
Bogus Identifications have actually ended up being a serious hazard in this digital period. Their illegal usage causes significant financial and also lawful damage to businesses, government companies and also individuals along with damaging communities and culture in its entirety. Counterfeit Identifications have actually even been linked to identity theft, human trafficking and bad acts – so it is crucial that you acquire reputable identification cards from a reliable vendor to avoid identification piracy, human trafficking or bad acts taking place utilizing phony records.
Before acquiring a counterfeit ID, it’s necessary to analyze its superior quality and look for any holograms. Poor quality IDs often feature telltale check in their manufacturing such as liquid chalking marks and also adhesive; in enhancement, these counterfeit records may be challenging to flex or squeeze due to being difficult plastic.
As even more teenagers attempt to acquire concocted Identifications online in order to celebration, it’s vital that they carry out thorough research in order to find a reliable seller as well as prevent entering any kind of difficulty as an outcome of obtaining a prohibited duplicate of ID. It will certainly stay clear of a large number of frustrations later on.
Counterfeit Identifications have come to be more prevalent than ever before in this period of electronic imitation. Teens as well as pre-college trainees can utilize counterfeit Identifications to enter bars where alcohol can not lawfully be consumed legitimately, get cigarettes and also other tobacco items and even accessibility financial assistance programs; all this task may develop severe lawful ramifications.
To address the problem, some companies are educating their cutting edge gatekeepers to acknowledge genuine as well as phony security qualities as well as behavioural nuances that makers can not evaluate – a vital step toward mitigating risk throughout person-to-person purchases. Some individuals recognize that, sometimes it might be required to register on websites with many individuals and make-believe data might wish to consider Romanian Fake Id.
When you know what to look for, identifying a false ID can be simple. A basic check of birth picture, date and name need to be sufficient; yet recognizing exactly what information to focus on can be invaluable. Pay specific attention to reliable aspects like color, holograms and also structure along with magnifier/light boxes which allow a closer assessment of an identification paper.
Counterfeit Identifications might appear harmless in the beginning, but their misuse can have major repercussions for those using them. A bouncer captured using false Identifications might deal with heavy penalties or prison time; additionally, having such IDs on file might taint their irreversible document permanently – nonetheless a qualified phony ID lawyer can assist mitigate damage as well as lessen effects.
Sham IDs present an increasing risk, not just in accessing restricted products and also services, but additionally for criminal objectives – human trafficking, trading exotic pets unlawfully, monetary fraud as well as identification piracy are simply a couple of instances of criminal activities that bogus IDs assist in. Plenty of organizations and also government workers who check Identifications as part of their work responsibilities just get 10 mins of training on just how to identify concocted Identifications.
Typical counterfeit ID problems include low top-caliber pictures, mismatched messages as well as smudged texts; unequal font spacing; uncomfortable letter positioning as well as lack of shade tinting are likewise among them. It is crucial to take into consideration just how the Identification really feels under stress as even convincing duplicates might crack or peel under stress and anxiety.
Plentiful individuals utilize fake IDs to avoid apprehension for alcohol consumption underage and also as an act of civil disobedience to protest a high legal age. The possible dangers linked with utilizing such IDs need to never be neglected: criminal fees, expensive legal costs and also discipline action from schools might take place as well as damages being done to local areas as well as culture as a whole.
Indications that an identification might be fraudulent consist of punctuation mistakes, smeared or fuzzy message and also rough or thick laminate. Likewise keep an eye out for safety components like state-specific watermarks or holograms as well as UV attributes with black light lighting.
If you are unclear whether an identification stands, ask the private to present an additional kind of id. If they decline, ask to leave your properties prior to reporting the incident with police authorities – this action is vital, considering that making use of counterfeit ID can have severe consequences.
 Stealthiness refers to the state or top quality of being undercover, discreet and peaceful; or being undercover, clandestine or underhanded.
Stealthiness refers to the state or top quality of being undercover, discreet and peaceful; or being undercover, clandestine or underhanded.
Stealth mode is a very useful means for start-ups to shield their intellectual building from burglary. This typically entails making all staff members authorize non-disclosure arrangements and alloting code names for brand-new projects; such procedures assist stay clear of early dismissals of suggestions while guarding patents against being replicated.
Undercover mode can also assist startups identify the proper market suitable for their products, yet can make increasing funds tough without disclosing info to prospective financiers. This can make testing models or collecting comments challenging to manage.
Businesses running in clandestinity modus might invest significant quantities of money when arising from it, on public connections projects that consist of holding an “Big Reveal” event and also talking to vital investors as well as owners, hiring added team in addition to expanding right into new areas – expenditures which may counter any perceived benefits of operating undercover.
Coworking areas have rapidly come to be preferred with small firms and remote employees seeking flexible workplace, networking opportunities as well as community support. Extra as well as extra forward-thinking corporations are likewise starting to use coworking spaces as a means of reducing extra workplace, accessing fresh talent pools while enhancing and also saving prices flexibility of expansion.
Coworking spaces might posture significant safety and privacy threats in spite of their appeal, due to their open formats which make it less complicated for criminals to snoop on employees’ displays as well as take sensitive information. This issue can be handled by seeing to it employees assess digital data or records secretive areas or installing laptop computer privacy filters which block sightseers from peering in on them while examining documents as well as data online.
Employees should prevent using the very same password across solutions and applications, employing a password supervisor can help them in creating more safe and secure yet easily-remembered passwords that secure their information safely in the cloud software that encrypts all of it.
Maintain Your Startup In Clandestinity Modus For a Short Period desfasoarters the capability to establish their speed as well as establish items gradually and also continuously while being protected from possible competitors and also able to observe the market to figure out staminas and weaknesses. This approach is particularly advantageous for state-of-the-art startups creating cutting-edge modern technologies not yet all set to expose.
Undercover mode provides additional time as well as resources for protecting licenses, which can commonly be time pricey as well as consuming to attain. Running under these situations reduces the threat of competitors swiping a suggestion prior to you introduce it yourself. Many people understand that, sometimes it may be required to sign up on internet sites with pretended detailed information and lots of people might wish to think about Finland fake Id…
One significant disadvantage of going right into undercover mode is a lack of market screening, which can cause producing products consumers do not wish or call for. To stop this from occurring, it is vital that comments be solicited early and also usually from individuals, although this does not need to take place in an indiscreet manner – there are different strategies for doing this without breaking secrecy.
Startups running in clandestinity mode need to concentrate on developing their products and also building a skilled team, while collecting responses from possible individuals without divulging personal information or the business tricks. There are several techniques available for doing this; UserTesting human understanding system can be utilized for gathering insight from possible customers about early concepts, properties or unreleased experiences without divulging individual information or identity details.
 Operating in stealth modus may be an advantageous strategy for startups with tried and tested market fit. Doing so allows them to establish items as well as solutions without worry of larger firms with more sources making use of their concepts or taking their intellectual building, saving both time as well as sources on items that do not fulfill genuine world requirements, working with only top talent without sustaining lawful responsibilities; as well as providing flexibility in locating top skill – vital components for success when running under clandestinity modus. For a startup operating under clandestinity modus to succeed. Recruiting group will certainly need be trustworthy and also highly seasoned people as component of success for any type of stealth mode startup organization running effectively under undercover modus.
Operating in stealth modus may be an advantageous strategy for startups with tried and tested market fit. Doing so allows them to establish items as well as solutions without worry of larger firms with more sources making use of their concepts or taking their intellectual building, saving both time as well as sources on items that do not fulfill genuine world requirements, working with only top talent without sustaining lawful responsibilities; as well as providing flexibility in locating top skill – vital components for success when running under clandestinity modus. For a startup operating under clandestinity modus to succeed. Recruiting group will certainly need be trustworthy and also highly seasoned people as component of success for any type of stealth mode startup organization running effectively under undercover modus.
Internet Data privacy does matter to most people. However the average person may be, innocently searching the web, without any realization of the information trail they are leaving behind. Well then, we have a concern for you … do you understand what web privacy is, and how the lack of it can affect your life?
Think of it … In a hyper-connected world moving at a speed we can hardly comprehend, web users are now dealing with more difficulties than ever. On the other, internet users are more exposed to security risks than ever.
Online safety and internet privacy are words swung around rather thoughtlessly these days, with really few individuals really knowing what privacy online is all about. In this digital age, without much understanding of how the web operates, you can be at risk of threatening your individual data.
In just a couple of words, web privacy describes just how much of your personal info remains private when you’re online. And by private info, we mean anything straight related to your personal life. This includes your house or work address, phone number, medical history, or list of contacts.
Eventually, it’s not just individual information that users share online. It’s also monetary data such as charge card or bank records. All these can quickly end up in the wrong hands, and lead to unfortunate circumstances where your cash or your identity get stolen. To respond to the concern “what is internet privacy,” we require to take a more detailed take a look at the exchange that takes place when we browse the web. Did you believe that using the internet is totally free? You are incorrect. Everything you do when surfing the web comes at a cost.
Whether you’re just visiting a web site and accepting its cookies, or sharing pictures with your followers on social media, keep in mind that a part of your personal information will no longer be only yours to understand. If the service you’re utilizing is free or not, it does not even matter. Everybody pays the very same cost of exposure. Often it may be essential to register on website or blogs with make-believe details and some may wish to contemplate Fake Id United Arab Emirates. It’s as simple as that! A website administrator will probably hate you for it, however who cares! It’s your information and personal information that is at stake!
Social networking and simply going online is nowadays an activity filled with dangers and dangers presented to our individual stability. People that care less about their online privacy and security might think that living in a digital world without stringent boundaries and constraints is not a big deal. However, internet privacy needs to be managed really thoroughly for everyone to feel just as safe as they would in real life.
If you consider it well, in your everyday life you don’t share your bank data or personal info with just about anybody. You expect people to appreciate your own privacy, and you respect theirs, and you don’t open the door of your house for any complete stranger to go into.
All things taken into consideration, the online medium needs to look the very same. We need much better privacy laws to protect us from unsolicited 3rd celebrations.
As we all understand, many apps demand to understand our location to give you even more access to their benefits and features. It’s not obligatory, for sure, but if you will permit just any app to track you without thinking twice, you risk sharing your area with third parties you have no concept about, and these consist of hackers too.
Awareness is advised as well as individual participation in the way all your app’s settings are adjusted. Social media are also a growing concern when it comes to sharing your place’s info. Many of the time, being on social media, consisting of the likes of TikTok, Facebook, Instagram, Twitter, or LinkedIn, means voluntarily publishing photos, videos, or tweets of yourself and filling in your existing place.
Social network is all fun and games until it’s not any longer, and the info you’ve voluntarily shared becomes a threat. When looking at what web privacy is, we need to go over the way online search engine such as Google or Yahoo save our data.
The search engines we all use maintain lots of info about ourselves, what we like to check out, what we like to buy, where we go on holiday, and so on, and there’s truly very little we can do to guide clear of this contemporary conundrum. As you’ve most likely currently seen, there are a lot of web sites and business out there that require your individual information to grant you access to their services. This information is usually not encrypted and, therefore, not secure, which means that anyone can read it.
Cybercriminals are more enticed than ever to break accounts and steal monetary and individual info given that security vulnerability is now a function of the online environment. When you are online, your activity and searching history is tracked and tape-recorded by different apps for a number of various factors.
And although the majority of the time the information they collect is used for advertising purposes, often it can end up in the hands of cybercriminals. Simply put, another online privacy concern we’re facing nowadays is the refined and continuous monitoring we’re all calmly subjected to.
The most crucial thing we hope you acquire from reading this post is the understanding that Internet privacy is worth safeguarding at all costs. Web privacy represents our sense of freedom, safety, and personal identity online and outside the internet.
Often having fun with an app’s privacy settings is simply insufficient and extended actions require to be taken to guard our well-deserved web privacy. It can be difficult to safeguard your privacy at times, but it’s a vital job. It can assist you avoid identity theft, doxing, and other problems that are prevalent online.
Dealing with a reputable group will use you answers to your concerns and offer feedback on privacy best practices. At Internet Privacy, we establish personalized online privacy plans that satisfy your online needs and keep you updated on your privacy security status.
Only by staying watchful about what you share and who you share with can you secure yourself from potential fraud, financial loss, and identity theft. Internet privacy is the retention of the personal data we shared online in a way that protects our privacy, similar to in real life. We need it, after all, to keep a sense of personal identity, even online, where every little details is shared. Having stated this, we must take all required actions to safeguard our internet privacy now, both at a societal level and a private one, prior to it’s too late.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, de-laminação e des-metalização e desbotamento precoce. Essa garantia não se aplica a defeitos na instalação, e manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto deverá ser feita com nota fiscal eletrônica de devolução com as características iguais a nota de venda. A garantia será feita somente no valor e quantidade dos produtos adquiridos, não sendo devolvido valores em espécie, somente em produtos e não contemplando a mão de obra de instalação.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto acompanhado de sua respectiva nota fiscal, modelo e transparência do material.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, delaminação e des-metalização, de materiais instalados conforme suas especificações e utilidades.
Esta garantia não se aplica a defeitos na instalação, bem como manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto instalado, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto para garantia deverá ser feita com nota fiscal eletrônica (emitida pela loja instaladora), com as características iguais a nota de venda.
A garantia será feita somente no valor e quantidade dos produtos adquiridos, não permeando valores de mão de obra de aplicação, e posteriormente o produto será encaminhado ao instalador para substituição.
