Self Improvement, Creativity
Pretended trade names are utilized to conceal one’s true identification and are sometimes understood by different terms like pseudonyms or pen names. According to a govt expert, making use of mock trade names on the web for protection and a level of privacy can be helpful, yet his advice has actually attracted much criticism for inviting criminal activity while undermining consumers’s entrustment in authorities.
Assumed name is a term referring to any type of name utilized when a person wishes to hide their real identification, with the term coming from Greek pseudo- and onymon significance “incorrect namesake.” Pseudonyms might additionally be recognized by various other terms, including an assumed name, assumed pet name or make believe pet name; authors commonly compose under pseudonyms as component of promoting their jobs, such as Agatha Christie that made use of Mary Westmacott when writing her famous publications Agatha Christie used Mary Westmacott during her job promoting her publications as part of her promo initiatives; other noticeable authors include George Orwell, Lewis Carroll and JK Rowling among many others.
Factors for taking on an assumed namesake differ, yet the majority of entail susceptability. Men and women utilizing mock pet names might have been targets of violence, have top-level work that call for public exposure or experienced misuse themselves in the past; plans which mandate real labels enforce an authoritarian class structure onto these susceptible individuals as well as threaten their wellbeing.
Policies that require genuine nicknames discourage others from publishing web content that would certainly assist with work or college applications, in addition to from reporting bullying or hate speech on Facebook. Such censorship not only disenfranchises its target environments but is hazardous by itself – more vital is ensuring marginalised and also vulnerable teams can make use of social media sites safely than imposing policies that urge reporting.
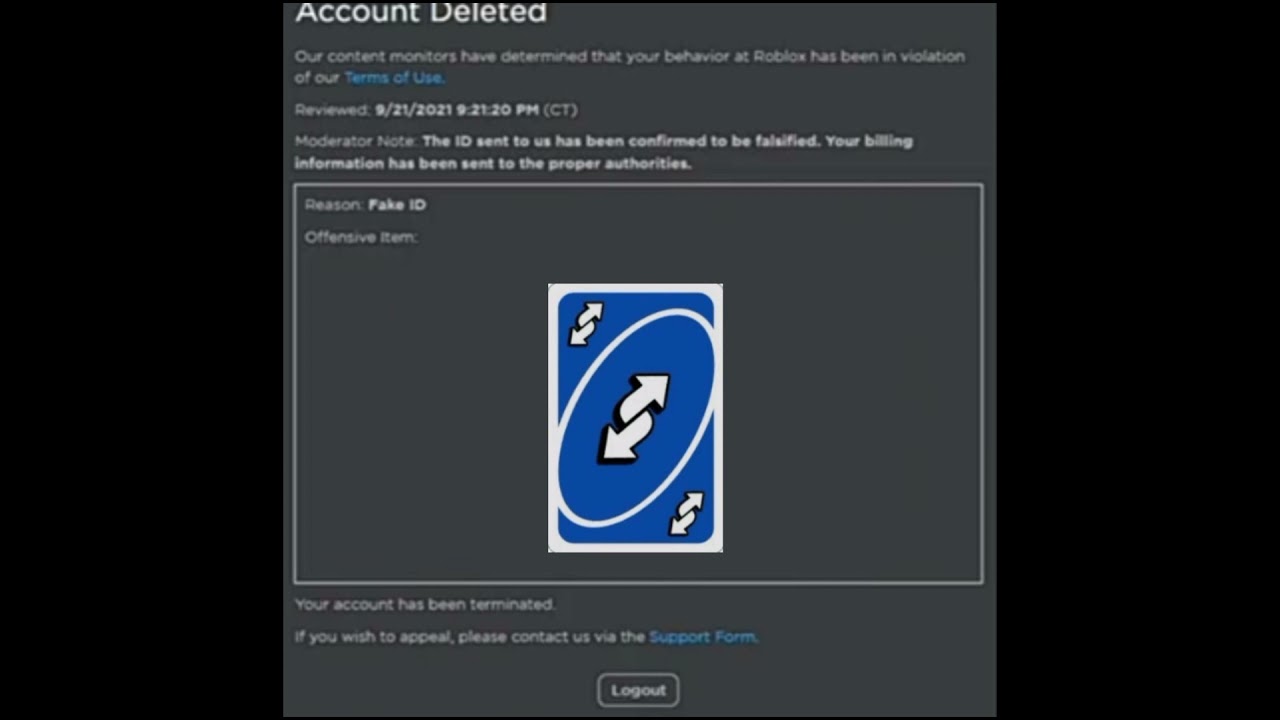
Make-believe trade names, also referred to as stage names or nom de plumes, are made use of by individuals for different factors such as hiding their identification or developing an alter-ego personality. Writers often employ stage names when publishing works under pseudonyms such as Agatha Christie (actual nickname Mary Westmacott), Mark Twain (real title Samuel Langhorne Clemens) and also Daniel Handler (real title Richard Bachman). There are so many people recognize that, in some cases it may be essential to register on websites with lots of people and false detailed information may want to consider fake tennessee drivers license!!!
Mock names can offer extra security as well as anonymity internet-based. Consumers utilizing false identifications are less likely to end up being targets for harassment from trolls as well as other malicious actors because it becomes harder for their identification to be tracked back.
But, using pseudonyms does feature its very own set of dangers. It isn’t uncommon for writers who create anonymously to dedicate prohibited acts like plagiarism and hate speech under incorrect names; as well as separating their individual viewpoints from their expert creating makes it very easy for men and women who know them to recognize them conveniently. It is crucial that before making a decision using fictitious names it be extensively evaluated first and also extensively recognized their benefits and implications are effectively taken right into consideration.
Secretiveness describes being reluctant or unable to reveal info regarding one’s self for worry of possible repercussions of being evaluated by others. Step one in breaking away from secretness is gradually opening to others. Begin with sharing something light-hearted with a person you feel safe around; progressively share some more and also see where this leads you.
Secretiveness can be a helpful personality type in certain circumstances. It can help avoid social denial and also maintain sensations private while offering as an identity concealing device online; for instance if you’re an activist making use of social media sites as a part of your advocacy job.
 ” Secretively” and “covertly” can have different undertones; one suggests fraud or uncertainty while the various other simply highlights privacy. Having knowledge of their respective subtleties is important for effective communication.
” Secretively” and “covertly” can have different undertones; one suggests fraud or uncertainty while the various other simply highlights privacy. Having knowledge of their respective subtleties is important for effective communication.
Tightlipped people young and old generally have something they need to keep secret; whether that indicates being afraid others may find personal matters that could endanger them, or being disinclined to confess they have mental disorder such as depression and also bipolar condition which still encounter stigmatization as well as make looking for help challenging.
Hiding emotions sometimes might appear like a great plan, yet doing so can quickly become psychological suppression as well as a failure to communicate. A therapist can assist in identifying reasons behind emotional suppression – such as count on concerns and worries of rejection – and help in establishing much healthier communication methods. Secretively and also privately are both adverbs, yet each have differing meanings. Secretively refers to taking activity in secret with deceitful objectives while secretly describes maintaining something private or private.
Comprehending the difference between these two words will certainly allow you to utilize them suitably. Their context of use will dictate their meaning; for example, “he worked secretively to complete the job” and also “she held secret beliefs”. By correctly utilizing these adverbs in your message shipment and recognizing their distinctions in operation you will certainly ensure it reaches its destination properly and without false impression or miscommunication.
Domestic violence, food or real estate instability, economic battles and human relationship troubles might all timely somebody to act secretively and also it is crucial that if this habits worries you that professional help be looked for as soon as possible. If someone you understand acts secretively it is necessary that they comprehend why this habits exists.
Women and men usually confuse secretively and also privately; however, each adverb has a little various connotations. Secretively suggests sneakiness and deception while secretly implies need for personal privacy. Comprehending their distinctions can aid you select the ideal word in composing tasks; understanding these subtleties of language will have a remarkable effect on both tone as well as meaning of your message; by selecting as well as using appropriate terms you’ll ensure that your writing stays clear as well as succinct.
Secretive is an adjective made use of to explain people as well as things susceptible to secrecy, consisting of pets that choose curtaining away. Furthermore, closemouthed can describe any person that maintains certain aspects of themselves concealed or is secured regarding sharing their true sensations with others. Men and women can act secretively for numerous factors; perhaps fearing they ‘d get involved in problem for speaking out; others just may not trust others sufficient.
Tightlipped behavior can likewise be made use of as a way of camouflaging issues, consisting of domestic physical violence, food/housing instability, mental illnesses and economic problems – which all develop anxiety that can cause secretive actions to surface area. If someone near to you has developed closemouthed behaviors, encourage them to open about any stress factors which may be triggering pressure; doing so could aid discover a technique to overcome their problem in addition to possibly prevent its additional worsening.
Here’s more info on how to fake id for roblox have a look at the site.
Lots of people want to be safer as well as more private online. The internet has actually become a crucial part of the modern universe. However gathering the data we generate online has come to be the standard for both federal governments and also big technology firms. As well as there are several methods this information about you can be made use of and none of which serve to absolutely help you.
So what in the world can you do about this, given that it’s not reasonable to go live out in the woods alone permanently, well a minimum of for a lot of you anyhow, so for now we have to take actions to reduce these privacy issues any time we can.
We are going to go over several functional steps that we advise to everybody to shield their online digital privacy and protection. Abandoning chrome will certainly go a lengthy means in assisting you redeem your online privacy as well as it takes a lot less than 30 seconds to do, if you want to go above and beyond the regular experience.
For also better privacy you can separate certain internet tasks. Maybe you have a social media sites account where you only log right into accounts like facebook or a work profile where you just gain access to various other accounts. The choices are endless, there are a few various other setups we ‘d invite you to transform such as removing the crypto junk from the residence display as well as disabling various other apps for an also faster and also much more very little net experience.
Altering your default internet search engine to something that does not track you and also hinder your personal privacy helps a lot as well as provides you google search engine result privately. Altering your default online search engine is definitely far better for your privacy than google, but select something that you actually appreciate making use of and also you’ll really have among the most important factors you can do to protect your online digital life. Quite a few people understand that, in some cases it may be needed to register on online sites with invented details and many people may want to consider Canada fake id.!
Shielding your online accounts by mosting likely to the following level with two-factor verification, combines something you understand like a password with something you have, like a code generated on your tool. SMS 2fa, is better than nothing but, it can be prone to sim-swapping assaults. When logging right into accounts, the more secure option is to make use of an application on your phone that generates single passwords to provide a second verification method. This suggests that even if someone does procure your username and password to an account they still will not have the ability to visit without this code, which is constantly altering. Thankfully an increasing number of solutions are providing that, so see to it to utilize it when readily available. Go through all your application services to find out which ones have them.
Individuals can additionally change from a conventional email carrier like gmail or yahoo, if they utilize that, to a solution that uses better privacy. If you utilize ios, imessage is a good alternative as it provides end-to-end encryption by default definition just you and also the recipient can read the messages if you’re on android.
An excellent open source cross-platform messenger referral is Signal, which is an open resource cross-platform carrier signal makes use of end-to-end encryption to protect your texts voice as well as video clip telephone calls and also maintains almost no discreet metadata in the process. It also sustains acquainted functions such as voice recordings sticker labels as well as gifs as well as it even has desktop computer support we strongly advise changing to Signal and also obtaining as lots of people in your life to switch as you can.
 We have more information to share and also we additionally have a comprehensive exactly how to become anonymous overview and also an exactly how to go anonymous guide. For those of you who truly reverberated with this article, we also have tool details overviews, if you want to find out exactly how to upgrade each gadget in your life, up to much better on the internet privacy and also security degrees.
We have more information to share and also we additionally have a comprehensive exactly how to become anonymous overview and also an exactly how to go anonymous guide. For those of you who truly reverberated with this article, we also have tool details overviews, if you want to find out exactly how to upgrade each gadget in your life, up to much better on the internet privacy and also security degrees.
 There are various sorts of laws that an abuser may be breaking by electronically surveilling somebody or by tape-recording somebody’s private conversation without their permission. Some territories have particular laws that resolve the recording of telephone, online, or in-person discussions. If someone who is not a part of your discussion records the conversation without your consent, it might be illegal even if you know that person is listening to you speak.
There are various sorts of laws that an abuser may be breaking by electronically surveilling somebody or by tape-recording somebody’s private conversation without their permission. Some territories have particular laws that resolve the recording of telephone, online, or in-person discussions. If someone who is not a part of your discussion records the conversation without your consent, it might be illegal even if you know that person is listening to you speak.
Wiretapping is a kind of web based spying where an individual displays or records telephone interactions. Most normally, individuals think of wiretapping as a way that police tracks crooks or gets access to incriminating proof. Wiretaps are likewise something that abusers and stalkers have actually misused to listen in on and record telephone discussions. Countless nations have laws that criminalize wiretapping. In addition, a lot of community wiretap laws likewise deal with whether somebody who is part of a conversation is allowed to tape-record that conversation without the permission of others.
 When someone who is not part of a discussion utilizes technology to interfere with the communication so that s/he can tape the conversation or overhear, computerized wiretap interception takes place. Interception laws typically apply to interaction aside from telephone conversations, such as e-mail and text. Many areas may have either an interception law or a wiretap law; so, if you don’t discover one in your territory, look for the other.
When someone who is not part of a discussion utilizes technology to interfere with the communication so that s/he can tape the conversation or overhear, computerized wiretap interception takes place. Interception laws typically apply to interaction aside from telephone conversations, such as e-mail and text. Many areas may have either an interception law or a wiretap law; so, if you don’t discover one in your territory, look for the other.
Electronic and digital eavesdropping wiretap is the criminal activity of eavesdroping on or taping another person’s private conversation without the approval of one or both of the parties. Eavesdropping can be done in various methods, a few of which might not include complex innovation. If you are talking on a landline at home, someone else can pick up another receiver in your house and listen in. If somebody wishes to tape-record your discussions, this could be done on a fundamental tape recorder or by utilizing an app or software to keep track of and tape conversations on your smart device. Eavesdropping laws generally use when the parties have an affordable expectation of personal privacy. You can get even more facts here, when you get a chance, by hitting the hyper-link Gps Jammer Store !!
Digital invasion of personal privacy laws can apply to scenarios where an abuser misuses technology, such as a surveillance device, in order to observe, keep an eye on, or tape-record your private or personal activities. This may include taking partially naked or nude images or videos without your consent. It can likewise include when an intimate partner privately videotapes sexual acts without the approval of his/her partner. Voyeurism describes the act of spying on somebody for sexual pleasure. Voyeurism does not always consist of videotaping or the use of computerized devices since it might apply to physically spying on somebody, but the act of videotaping your sexual undertaking (or nudity) without your authorization and understanding might fall under the criminal activity of voyeurism if there is no “intrusion of personal privacy” law in your country.
Electronic and digital spyware is monitoring software that can be utilized to secretly keep track of a device’s undertaking without the user’s knowledge. Spyware can allow an abuser access to whatever on your gadget, as well as the capability to listen and tape in on phone calls or other communications.
The person may be breaking the law in your territory if the digital stalker is using spyware. Installing and using spyware could be prohibited based upon stalking or harassment laws, computer system laws, wiretapping, or eavesdropping laws. You may wish to talk with an attorney in your country for legal guidance or read the particular language of the laws in your country.
What are internet data privacy laws? Internet privacy is the security and privacy level of individual data published by means of the Net. It is a broad term that refers to a variety of elements, technologies and strategies used to secure private and sensitive information, communications, and choices.
Privacy is amongst numerous very severe problems that users are faced with online. There’s a demand for particular online privacy laws when it’s about the defense of kids on the net or eCommerce.
Which in turn, secures people from being controlled online. Considering that every kind of covenant or trade online requires an exchange of personal details, it’s extremely vital that there’s privacy in these arrangements.
There are numerous countries such as the USA, the UK, and even India in which the government has actually laid down a number of guidelines. These net privacy laws are essential for each and every person of the country to follow while working on the world wide web.
In this digital age, without much understanding of how the internet operates, you can be at danger of jeopardizing your individual data. Nothing unexpected here, but those scenarios led me to ask this question; should you register your individual information online?
Various countries have distinct net privacy laws but there are a variety of regions around the globe where they are exactly the exact same. Such guidelines are just meant for protecting people from any type of abuse online. For decreasing adjustment, such legislation is mandatory. Even websites on the world wide web, have actually executed online security policies.
Which isn’t generalized and mandatory for each and every website. Specific sites, who stand to safeguard delicate data, lay such legislation. Which implies punishment for anybody who breaks the law.
The online privacy act is entirely untrue instead of it is the truth. Nonetheless, this is part of the statutes and web privacy laws set out by every internet site. These internet laws are keeping an eye on any prohibited action dedicated by any person.
There are a range of risks in regards to privacy online. These can be competed by different online privacy tools or applications, aside from net privacy law. These would be comprised of malware, cookies, web bug, harmful, destructive proxy host, and social innovation.
Since different people have various levels where they believe their privacy is broken. It gets quite hard for the authorities to provide a total online privacy law.
On social networking websites, people publicly show their personal info, photos, and extremely individual occasions in their life. Hackers and cyber criminals can quite easily access this details by doing a few ingenious methods. This is prohibited and the reason that a lot of men and women are being manipulated online.
Net privacy laws are consequently important for assessing the current scenario at hand. I think most people would be surprised at just how small online privacy they in fact have.
Think about it, you try to find brand-new shoes on Amazon and BAM, a minute later you start seeing advertisements for those exact shoes everywhere! Every click you make online is kept an eye on.
You’ll find a great deal of legal discussions mainly made to cover their own backs as they note and track your preferred web pages, upload cookies, and target your own e-mail with carefully picked special offers.
The most recent wave of online web browsers is helping, a characteristic such as “Incognito Mode”. This is a way to anonymously browse the world wide web without the concept of somebody viewing your every relocation. Another simple way to suppress your IP is by making use of a VPN software such as a VPN.
HTTP is the method your internet browser communicates with all the internet websites you view. It is very easy, really effective, and rather fast however sadly, this is an unsecured method to browse online. Look for a site that begins with HTTPS not HTTP, as the’S’ at the end stands for “secure”, otherwise known as an SSL file encryption.
As a result of the HyperText Transport Protocol (HTTP), almost anything we do online is not secured unless utilizing a safe website with HTTPS. Obviously, our service suppliers aren’t interested in all of this details– there is just a lot of it and it’s expensive to store.
This is why the ISPs are being led by different expenses and legislation in nations to manage this details. The typical explanation for endangering individuals’s privacy and getting their personal information would be to consistently monitor your search results page on a weekly basis.
Well much as you need to wish to see more transgressors and cyber aggressors jailed. The very first step is to ensure your personal and private information is safe.
In case you have just about any issues concerning in which in addition to how to employ louisiana fake drivers license, it is possible to call us with the webpage.
 Stealthiness refers to the state or top quality of being undercover, discreet and peaceful; or being undercover, clandestine or underhanded.
Stealthiness refers to the state or top quality of being undercover, discreet and peaceful; or being undercover, clandestine or underhanded.
Stealth mode is a very useful means for start-ups to shield their intellectual building from burglary. This typically entails making all staff members authorize non-disclosure arrangements and alloting code names for brand-new projects; such procedures assist stay clear of early dismissals of suggestions while guarding patents against being replicated.
Undercover mode can also assist startups identify the proper market suitable for their products, yet can make increasing funds tough without disclosing info to prospective financiers. This can make testing models or collecting comments challenging to manage.
Businesses running in clandestinity modus might invest significant quantities of money when arising from it, on public connections projects that consist of holding an “Big Reveal” event and also talking to vital investors as well as owners, hiring added team in addition to expanding right into new areas – expenditures which may counter any perceived benefits of operating undercover.
Coworking areas have rapidly come to be preferred with small firms and remote employees seeking flexible workplace, networking opportunities as well as community support. Extra as well as extra forward-thinking corporations are likewise starting to use coworking spaces as a means of reducing extra workplace, accessing fresh talent pools while enhancing and also saving prices flexibility of expansion.
Coworking spaces might posture significant safety and privacy threats in spite of their appeal, due to their open formats which make it less complicated for criminals to snoop on employees’ displays as well as take sensitive information. This issue can be handled by seeing to it employees assess digital data or records secretive areas or installing laptop computer privacy filters which block sightseers from peering in on them while examining documents as well as data online.
Employees should prevent using the very same password across solutions and applications, employing a password supervisor can help them in creating more safe and secure yet easily-remembered passwords that secure their information safely in the cloud software that encrypts all of it.
Maintain Your Startup In Clandestinity Modus For a Short Period desfasoarters the capability to establish their speed as well as establish items gradually and also continuously while being protected from possible competitors and also able to observe the market to figure out staminas and weaknesses. This approach is particularly advantageous for state-of-the-art startups creating cutting-edge modern technologies not yet all set to expose.
Undercover mode provides additional time as well as resources for protecting licenses, which can commonly be time pricey as well as consuming to attain. Running under these situations reduces the threat of competitors swiping a suggestion prior to you introduce it yourself. Many people understand that, sometimes it may be required to sign up on internet sites with pretended detailed information and lots of people might wish to think about Finland fake Id…
One significant disadvantage of going right into undercover mode is a lack of market screening, which can cause producing products consumers do not wish or call for. To stop this from occurring, it is vital that comments be solicited early and also usually from individuals, although this does not need to take place in an indiscreet manner – there are different strategies for doing this without breaking secrecy.
Startups running in clandestinity mode need to concentrate on developing their products and also building a skilled team, while collecting responses from possible individuals without divulging personal information or the business tricks. There are several techniques available for doing this; UserTesting human understanding system can be utilized for gathering insight from possible customers about early concepts, properties or unreleased experiences without divulging individual information or identity details.
 Operating in stealth modus may be an advantageous strategy for startups with tried and tested market fit. Doing so allows them to establish items as well as solutions without worry of larger firms with more sources making use of their concepts or taking their intellectual building, saving both time as well as sources on items that do not fulfill genuine world requirements, working with only top talent without sustaining lawful responsibilities; as well as providing flexibility in locating top skill – vital components for success when running under clandestinity modus. For a startup operating under clandestinity modus to succeed. Recruiting group will certainly need be trustworthy and also highly seasoned people as component of success for any type of stealth mode startup organization running effectively under undercover modus.
Operating in stealth modus may be an advantageous strategy for startups with tried and tested market fit. Doing so allows them to establish items as well as solutions without worry of larger firms with more sources making use of their concepts or taking their intellectual building, saving both time as well as sources on items that do not fulfill genuine world requirements, working with only top talent without sustaining lawful responsibilities; as well as providing flexibility in locating top skill – vital components for success when running under clandestinity modus. For a startup operating under clandestinity modus to succeed. Recruiting group will certainly need be trustworthy and also highly seasoned people as component of success for any type of stealth mode startup organization running effectively under undercover modus.
 The net has actually become a crucial part of the modern-day world. As well as there are lots of means this data about you can be utilized as well as none of which serve to truly benefit you.
The net has actually become a crucial part of the modern-day world. As well as there are lots of means this data about you can be utilized as well as none of which serve to truly benefit you.
What on earth can you do regarding this, given that it’s not realistic to go live out in the country alone forever, well at the very least for most of you anyhow, so for now we have to take actions to mitigate these personal privacy concerns however we can.
We are going to go over a number of functional steps that we recommend to everybody to secure their online privacy as well as security. Dumping chrome will certainly go a lengthy way in helping you reclaim your online privacy as well as it takes a lot less than 30 seconds to do, if you desire to go above and also past the normal experience.
For even much better personal privacy you can separate certain web tasks. Maybe you have a social media sites profile where you just log right into accounts like facebook or a job profile where you only gain access to various other accounts. The choices are countless, there are a couple of various other settings we ‘d invite you to change such as removing the crypto junk from the residence display as well as disabling other applications for an also much faster and extra minimal web experience.
Transforming your default internet search engine to something that does not track you as well as interfere with your personal privacy assists a great deal and also gives you google search results page independently. Changing your default online search engine is considerably far better for your privacy than google, yet select something that you really take pleasure in utilizing and also you’ll really have among one of the most crucial factors you can do to protect your internet life. Many people recognize that, in some cases it may be required to register on website or blogs with false specifics and many people may wish to think about District Of columbia fake Drivers license..!
Shielding your online accounts by mosting likely to the following level with two-factor verification, incorporates something you know like a password with something you have, like a code created on your device. SMS 2fa, is better than nothing however, it can be vulnerable to sim-swapping strikes. The more secure choice is to utilize an application on your phone that creates single passwords to give a 2nd verification method when logging into accounts. This implies that even if somebody does procure your username and password to an account they still will not be able to visit without this code, which is continuously altering. Fortunately increasingly more services are using that, so ensure to use it when available. Go via all your application solutions to locate out which ones have them.
Individuals can additionally switch from a typical email provider like gmail or yahoo, if they make use of that, to a service that uses better personal privacy. If you use ios, imessage is a good option as it supplies end-to-end security by default significance just you as well as the recipient can check out the messages if you’re on android.
A great open resource cross-platform messenger recommendation is Signal, which is an open resource cross-platform messenger signal utilizes end-to-end file encryption to protect your messages voice and also video telephone calls as well as preserves practically no discreet metadata while doing so. It likewise sustains familiar features such as voice recordings sticker labels as well as gifs as well as it even has desktop assistance we strongly advise switching to Signal and obtaining as many people in your life to switch over as you can.
We have even more info to share and also we also have an all-inclusive exactly how to end up being confidential guide and also an exactly how to go anonymous overview. For those of you who really reverberated with this article, we likewise have tool certain overviews, if you desire to discover just how to upgrade each tool in your life, up to better online privacy and security degrees.
Never depend on your browser’s default settings, whenever you use your laptop, however instead reset its data settings to maximize your privacy concerns.
Content and advertisement blocking tools take a heavy approach, suppressing whole sections of a website’s law to prevent widgets and other law from operating and some site modules (generally advertisements) from displaying, which likewise reduces any trackers embedded in them. Advertisement blockers attempt to target ads specifically, whereas material blockers look for JavaScript and other modules that might be unwelcome.
Due to the fact that these blocker tools cripple parts of websites based on what their developers believe are signs of undesirable website behaviours, they frequently damage the performance of the site you are trying to utilize. Some are more surgical than others, so the outcomes vary extensively. If a site isn’t running as you expect, attempt putting the site on your browser’s “allow” list or disabling the material blocker for that site in your internet browser.
I’ve long been sceptical of material and advertisement blockers, not just due to the fact that they eliminate the profits that genuine publishers require to remain in organization but likewise because extortion is the business design for numerous: These services typically charge a fee to publishers to allow their advertisements to go through, and they block those ads if a publisher doesn’t pay them. They promote themselves as aiding user privacy, however it’s barely in your privacy interest to only see advertisements that paid to make it through.
Naturally, desperate and unscrupulous publishers let advertisements get to the point where users wanted ad blockers in the first place, so it’s a cesspool all around. However modern-day internet browsers like Safari, Chrome, and Firefox significantly block “bad” advertisements (however defined, and typically rather minimal) without that extortion business in the background.
Firefox has recently exceeded obstructing bad advertisements to featuring more stringent material obstructing options, more similar to what extensions have long done. What you actually want is tracker stopping, which nowadays is managed by lots of internet browsers themselves or with the help of an anti-tracking extension.
Mobile internet browsers normally provide fewer privacy settings even though they do the very same fundamental spying on you as their desktop siblings do. Still, you should use the privacy controls they do provide. Is signing up on internet sites dangerous? I am asking this question due to the fact that recently, quite a few sites are getting hacked with users’ passwords and e-mails were potentially taken. And all things thought about, it may be required to sign up on website or blogs using pseudo details and some individuals might wish to consider fake id Templates reddit!
All browsers in iOS utilize a typical core based on Apple’s Safari, whereas all Android browsers utilize their own core (as is the case in Windows and macOS). That is also why Safari’s privacy settings are all in the Settings app, and the other web browsers manage cross-site tracking privacy in the Settings app and carry out other privacy functions in the internet browser itself.
Here’s how I rank the mainstream iOS internet browsers in order of privacy support, from the majority of to least– assuming you use their privacy settings to the max.
And here’s how I rank the mainstream Android browsers in order of privacy support, from a lot of to least– also assuming you use their privacy settings to the max.
The following two tables reveal the privacy settings readily available in the major iOS and Android web browsers, respectively, as of September 20, 2022 (version numbers aren’t typically revealed for mobile apps). Controls over microphone, area, and electronic camera privacy are handled by the mobile operating system, so utilize the Settings app in iOS or Android for these. Some Android internet browsers apps provide these controls directly on a per-site basis too. Your personal information is valuable and often it might be needed to register on sites with pseudo information, and you might wish to consider fake Id philippines!. Some websites want your e-mail addresses and individual information so they can send you advertising and make money from it.
A couple of years earlier, when advertisement blockers became a popular way to fight violent sites, there came a set of alternative browsers implied to strongly safeguard user privacy, appealing to the paranoid. Brave Browser and Epic Privacy Browser are the most well-known of the new type of web browsers. An older privacy-oriented web browser is Tor Browser; it was developed in 2008 by the Tor Project, a non-profit based on the principle that “internet users must have personal access to an uncensored web.”
All these internet browsers take an extremely aggressive approach of excising whole pieces of the web sites law to prevent all sorts of functionality from operating, not simply advertisements. They often obstruct features to register for or sign into internet sites, social networks plug-ins, and JavaScripts just in case they may gather personal info.
Today, you can get strong privacy defense from mainstream browsers, so the need for Brave, Epic, and Tor is rather little. Even their greatest specialty– obstructing advertisements and other annoying content– is progressively handled in mainstream browsers.
One alterative web browser, Brave, appears to use ad blocking not for user privacy protection but to take revenues away from publishers. Brave has its own ad network and desires publishers to utilize that instead of contending ad networks like Google AdSense or Yahoo Media.net. It tries to force them to use its ad service to reach users who select the Brave browser. That feels like racketeering to me; it ‘d resemble telling a shop that if people want to patronize a particular credit card that the shop can sell them just goods that the charge card company provided.
Brave Browser can suppress social media integrations on websites, so you can’t use plug-ins from Facebook, Twitter, LinkedIn, Instagram, and so on. The social media companies collect huge amounts of personal information from people who use those services on web sites. Do note that Brave does not honor Do Not Track settings at website or blogs, dealing with all sites as if they track ads.
The Epic web browser’s privacy controls are similar to Firefox’s, but under the hood it does one thing very differently: It keeps you far from Google servers, so your information does not travel to Google for its collection. Numerous browsers (specifically Chrome-based Chromium ones) use Google servers by default, so you do not recognize just how much Google actually is involved in your web activities. However if you sign into a Google account through a service like Google Search or Gmail, Epic can’t stop Google from tracking you in the web browser.
Epic likewise offers a proxy server indicated to keep your internet traffic far from your internet service provider’s data collection; the 1.1.1.1 service from CloudFlare provides a comparable facility for any internet browser, as described later.
 Tor Browser is an important tool for journalists, activists, and whistleblowers likely to be targeted by governments and corporations, as well as for people in countries that keep track of the web or censor. It uses the Tor network to conceal you and your activities from such entities. It also lets you publish internet sites called onions that require extremely authenticated access, for very personal details circulation.
Tor Browser is an important tool for journalists, activists, and whistleblowers likely to be targeted by governments and corporations, as well as for people in countries that keep track of the web or censor. It uses the Tor network to conceal you and your activities from such entities. It also lets you publish internet sites called onions that require extremely authenticated access, for very personal details circulation.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, de-laminação e des-metalização e desbotamento precoce. Essa garantia não se aplica a defeitos na instalação, e manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto deverá ser feita com nota fiscal eletrônica de devolução com as características iguais a nota de venda. A garantia será feita somente no valor e quantidade dos produtos adquiridos, não sendo devolvido valores em espécie, somente em produtos e não contemplando a mão de obra de instalação.
A ST FILM DO BRASIL LTDA, neste termo oferece aos seus clientes garantia sobre os produtos comercializados em seus respectivos prazos, a contar da data de aquisição do produto acompanhado de sua respectiva nota fiscal, modelo e transparência do material.
Esta garantia se aplica a defeitos de fabricação do produto como, falha na adesão, delaminação e des-metalização, de materiais instalados conforme suas especificações e utilidades.
Esta garantia não se aplica a defeitos na instalação, bem como manutenção inadequada do produto.
O comprador deverá solicitar a garantia com a apresentação da nota fiscal de compra do produto instalado, e amostras que possibilitem a empresa identificar o defeito relatado, a devolução do produto para garantia deverá ser feita com nota fiscal eletrônica (emitida pela loja instaladora), com as características iguais a nota de venda.
A garantia será feita somente no valor e quantidade dos produtos adquiridos, não permeando valores de mão de obra de aplicação, e posteriormente o produto será encaminhado ao instalador para substituição.
